Search for "Bent" returned 1925 results

32 min
Why Do We Anthropomorphize Computers?...
...and dehumanize ourselves in the process?

41 min
Extracting keys from FPGAs, OTP Tokens and Door Locks
Side-Channel (and other) Attacks in Practice
52 min
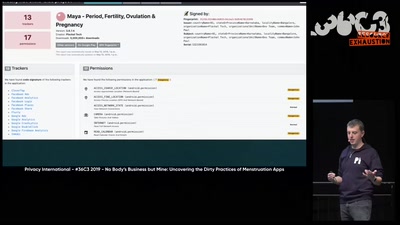
No Body's Business But Mine, a dive into Menstruation Apps
The Not-So Secret Data Sharing Practices Of Menstruation…

58 min
The Magic World of Searchable Symmetric Encryption
A brief introduction to search over encrypted data
61 min
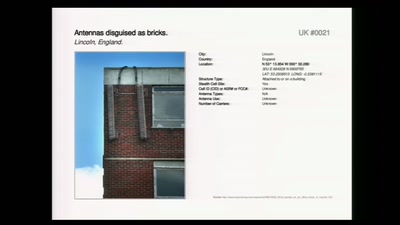
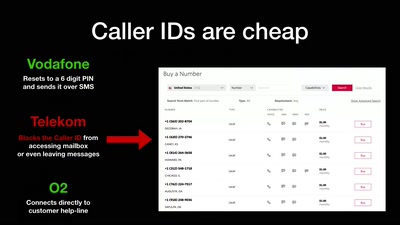
The architecture of a street level panopticon
How drones, IMSI Catchers, and cameras are shaping our…

36 min
Modchips of the State
Hardware implants in the supply-chain

63 min
Don't stop 'til you feel it
Artistic interventions in climate change
39 min
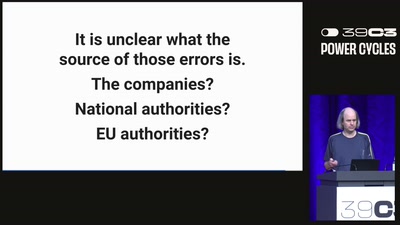
Greenhouse Gas Emission Data
Public, difficult to access, and not always correct
63 min
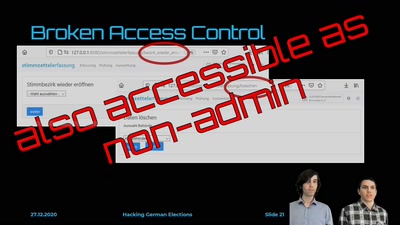
Hacking German Elections
Insecure Electronic Vote Counting - How It Returned and Why…

60 min
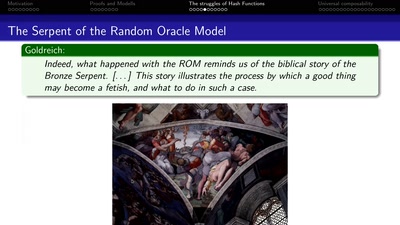
Quantum Cryptography
from key distribution to position-based cryptography
60 min
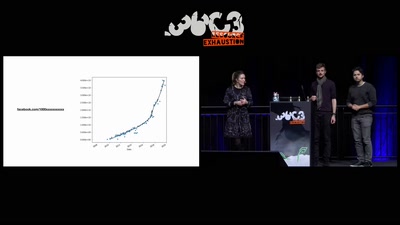
Inside the Fake Like Factories
How thousands of Facebook, You Tube and Instagram pages…
60 min
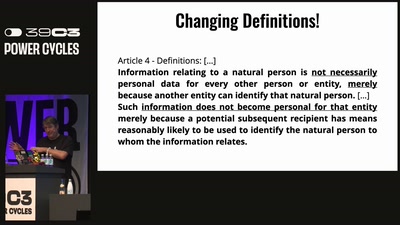
Throwing your rights under the Omnibus
How the EU's reform agenda threatens to erase a decade of…
63 min
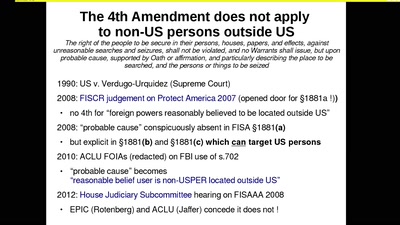
The Cloud Conspiracy 2008-2014
how the EU was hypnotised that the NSA did not exist
59 min