Search for "M" returned 12243 results
47 min
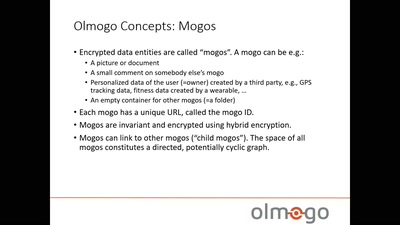
Olmogo - because it's your data!
A cryptographically secure social network platform

59 min
Developments in Coordinated Vulnerability Disclosure
The government is here to help
63 min
Data Exploitation
how your digital doppelganger has been exploiting you all…
61 min
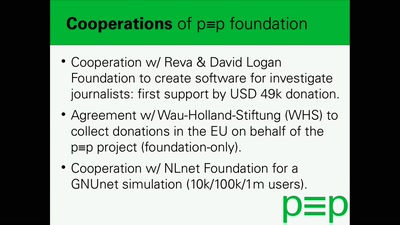
The state of the pretty Easy privacy (p≡p) project and what to expect next
Easy to use automatic encryption for the masses
25 min
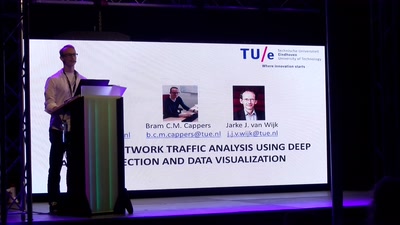
Network Traffic Analysis using Deep Packet Inspection and Data Visualization
Eventpad: the Sublime editor for network traffic
60 min
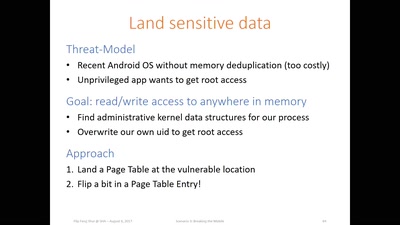
Flip Feng Shui
Advanced Rowhammer exploitation on cloud, desktop, and…
29 min
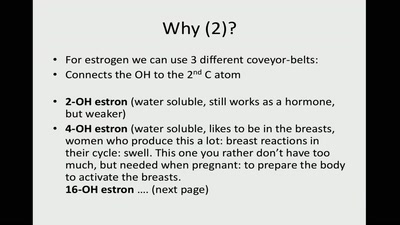
Hormones and Hysteria - what every person should know
are you not curious now? ;)
40 min
The World in 24 Hours Revisited
How to re-enact a 1982 network art performance
59 min
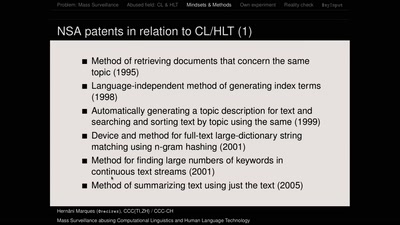
Mass Surveillance abusing Computational Linguistics and Human Language Technology
Mind-sets, state-of-the-art methods and practices according…
36 min
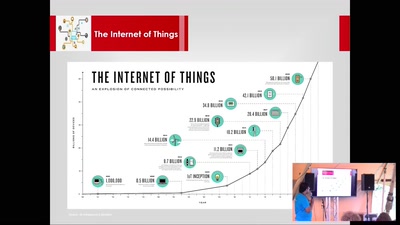
Smart Home Security with Tor
Using TOR for securing Smart Homes from prying eyes
52 min
An academic's view to incident response
It's all fun and games until reality starts kicking you in…
33 min
Social cooling
How the reputation economy is turning us into conformists

50 min
Art Tech Activism Privacy and Cool Robots
Not only hackers do Security, Privacy and Hacking. Want to…
27 min
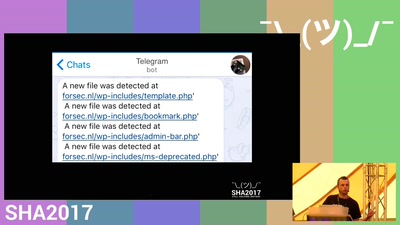
Detecting a breach from an attackers perspective.
We're gonna regret this

43 min
Hack North Korea
Flash Drives for Freedom
40 min
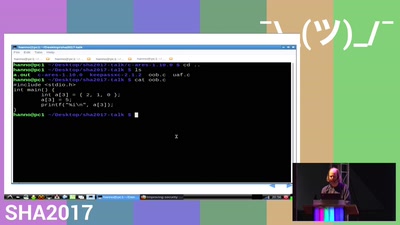
Improving security with Fuzzing and Sanitizers
Free and open source software has far too many security…
52 min
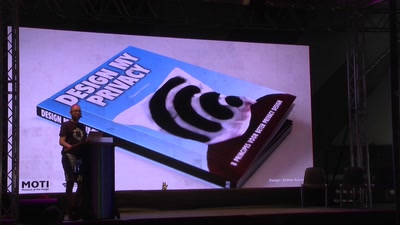
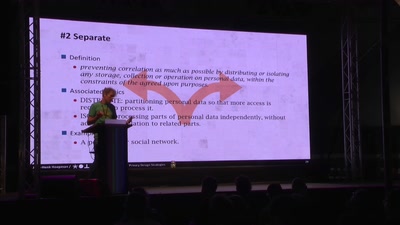
Privacy Design Strategies
Doing well is good enough
58 min
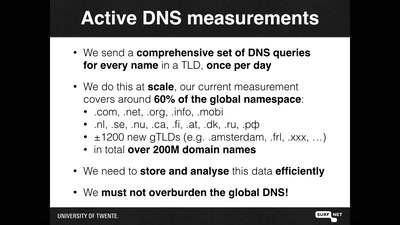
OpenINTEL: digging in the DNS with an industrial size digger
I measured 60% of the DNS, and I found this
61 min