Search for ">Y<" returned 10981 results
61 min
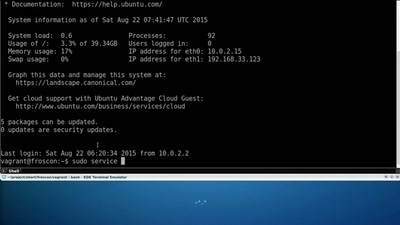
Drive-by SSL certificate creation with nginx
Explore the possibilities of a scriptable webserver
60 min
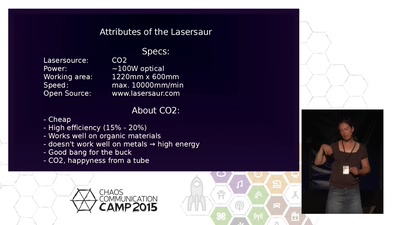
Living with the lasersaur
Experiences with the open source laser cutter
42 min
Let's Encrypt
A Certificate Authority To Encrypt the Entire Web
59 min
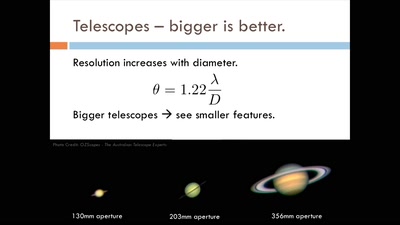
Detecting echoes from the dawn of time
Nifty technologies behind the world's most sensitive…
30 min
Satellite Imagery in Agriculture
Questioning privacy, data protection, and autonomy in the…
30 min
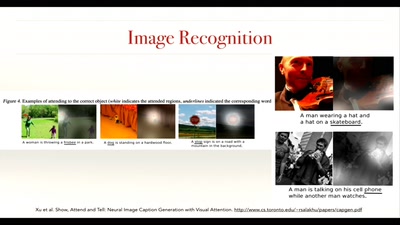
The quest for artificial general intelligence
beyond the Turing test
52 min
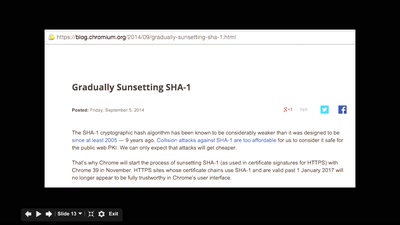
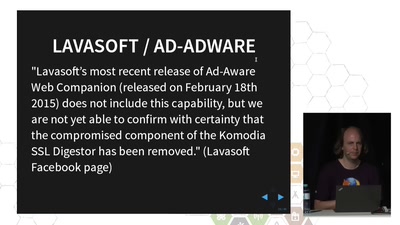
TLS interception considered harmful
How Man-in-the-Middle filtering solutions harm the security…
58 min
How to Destroy a Laptop with Top Secrets
How did GCHQ do it to the Guardian's copy of Snowden's…

45 min
Fueling the Revolution
Personal production of bio-fuels
56 min
Helping the Helpless
Targeted threats to civil society
27 min
Experimental Fermentation Institutes Network (EFIN)
fermenting together for better future
28 min
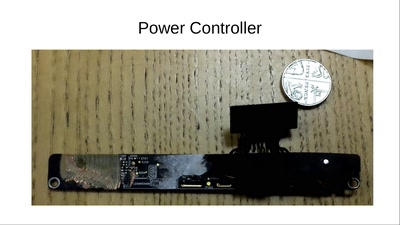
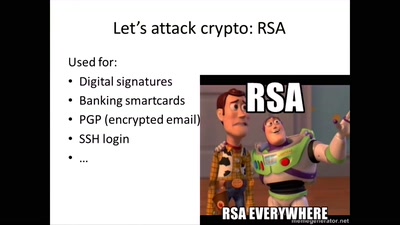
Hardware attacks: hacking chips on the (very) cheap
How to retrieve secret keys without going bankrupt
60 min
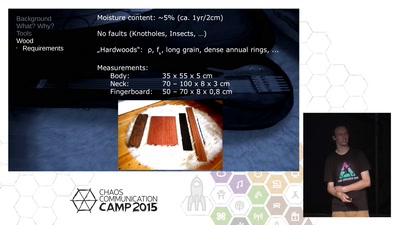
A Hackers Approach To Building Electric Guitars
Let's do everything except the pots by ourselves
![for women in "${tech[@]}"; do](https://static.media.ccc.de/media/conferences/camp2015/6774-hd.jpg)
26 min
for women in "${tech[@]}"; do
Let's talk, share and learn from each other.
28 min
Gotta Block’em all
Creating a usable tool against online trackers
26 min
Data and discrimination: representing marginalised communities in data
The right to be counted, or the right to be left alone?

27 min
Analogue Mission Simulations
Wait what? Why not digital?

69 min
The hills are alive with the sound of hacking ... don't wake the monkeys!
The State of the Hack in India. A place to be^W hack in the…
60 min
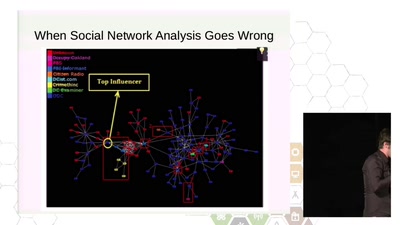
Resisting Surveillance: it's is not just about the metadata
The infiltration and physical surveillance of social…
46 min
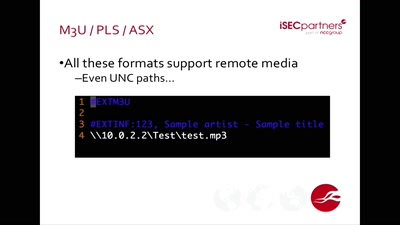
Bugged Files
Is Your Document Telling on You?
30 min