Search for "Ben" returned 9329 results

55 min
Technological art off the trodden tracks
Artists (mis)using technology

57 min
Rapid Prototype Your Life
The time is now to make anything you can imagine

49 min
Hacking Data Retention
How bureaucrats fail to fight terror
58 min
Geocaching and Alternate Reality Games
Play Simulations of Future Problems

60 min
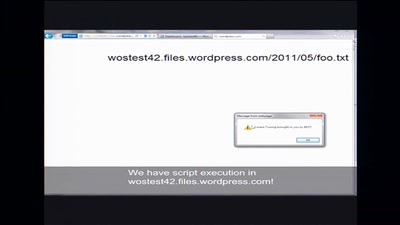
Exploring Protocols and Services on Internet Connected Embedded Devices
Looking for Insecurities
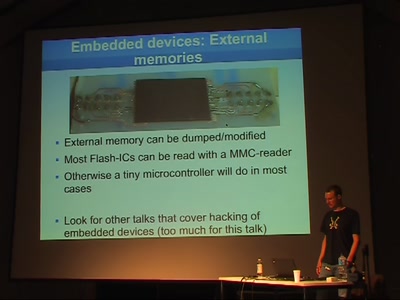
45 min
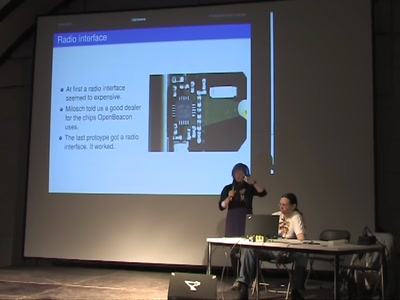
Machine-to-machine (M2M) security
When physical security depends on IT security
47 min
From robot to robot
Restoring creativity in school pupils using robotics

47 min
Software Patenting
Adequate means of protection for software.

62 min
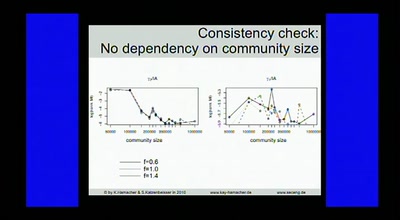
Detecting temperature through clock skew
Hot or Not: Defeating anonymity by monitoring clock skew to…
67 min
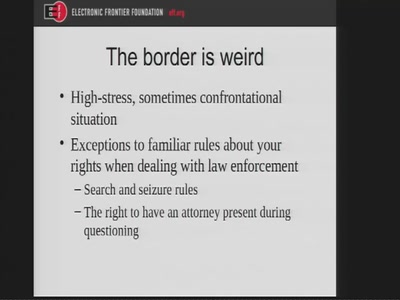
Laptop and Electronics Searches at the U.S. Border
A Privacy Guide for Travelers
47 min
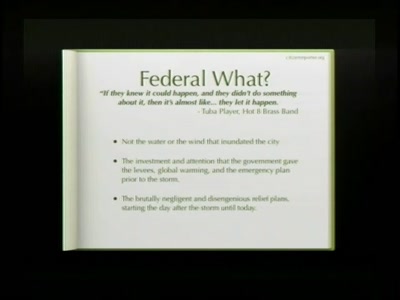
Rebellious Communication and the Federal Flood
My experience and the role of bloggers, podcasters, and…

49 min
VoIPhreaking
Introduction to SIP Hacking
33 min
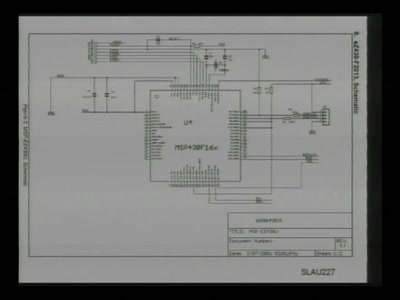
Repurposing the TI EZ430U
with msp430static, solder, and syringe

37 min
Hacking Space
Cheap access to Space using lighter then air methods

47 min
Peer-to-peer under the hood
An in-depth look at p2p algorithmics
47 min
Hacking the Bionic Man
Science fiction or security in 2040?
28 min
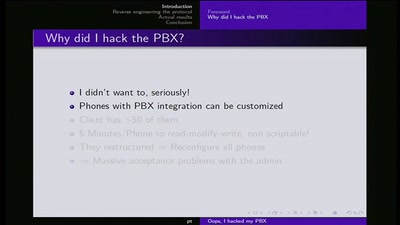
Ooops I hacked my PBX
Why auditing proprietary protocols matters

53 min
Automated Botnet Detection and Mitigation
How to find, invade and kill botnets automated and…
49 min
Safecast: DIY and citizen-sensing of radiation
Empowering citizen in the wake of Fukushima triple-meltdown…
35 min
Tricks: makes you smile
A clever or ingenious device or expedient; adroit…
43 min
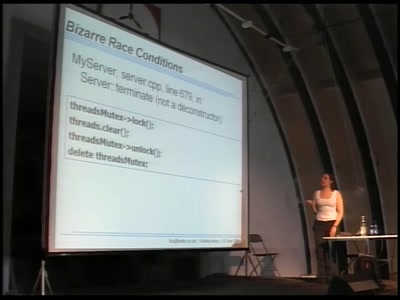
Twisting timing in your favour
Finding and exploiting concurrency issues in software
134 min