Search for ">Y<" returned 10982 results
30 min
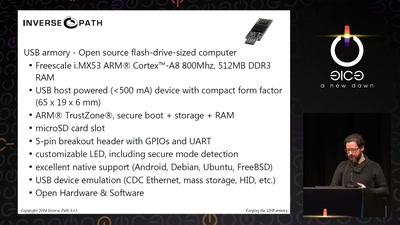
Forging the USB armory
Creating an open source secure flash-drive-sized computer
31 min
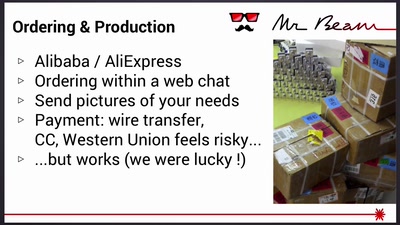
Mr Beam goes Kickstarter
Lessons learned from crowdfunding a hardware project
28 min
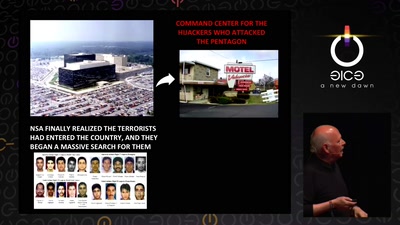
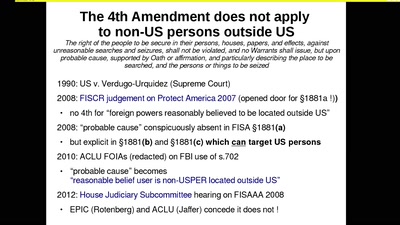
Long war tactics
or how we learned to stop worrying and love the NSA

32 min
Finding the Weak Crypto Needle in a Byte Haystack
Automatic detection of key-reuse vulnerabilities
31 min
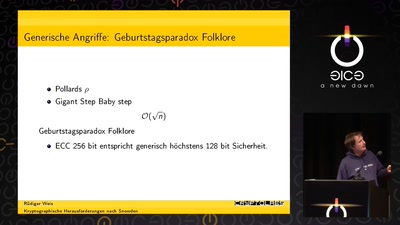
Krypto für die Zukunft
Verteidigung gegen Dunkle Künste
32 min
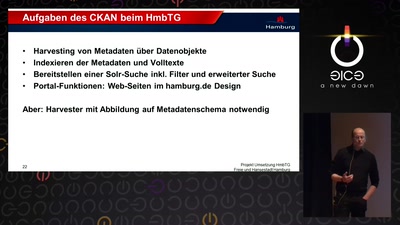
Das Transparenzportal Hamburg
Inhalt und Umsetzung
31 min
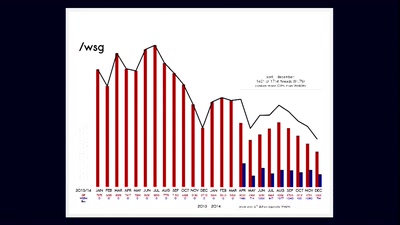
GIFs: Tod eines Mediums. Und sein Leben nach dem Tod.
Wie es kommt, dass technischer Fortschritt den Nutzern…
39 min
The automobile as massive data gathering source and the consequences for individual…
The next big privacy heist
55 min
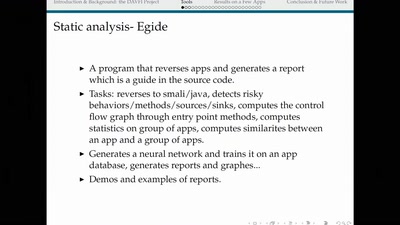
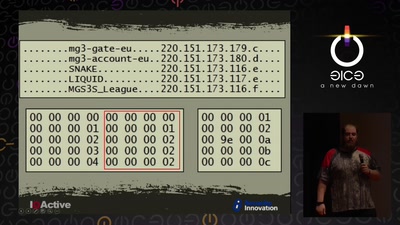
Cyber Necromancy
Reverse Engineering Dead Protocols

45 min
Serenität – Anleitung zum Glücklichsein
Das Duo 'read & delete' präsentiert radikale philosophische…
62 min
Tell no-one
A century of secret deals between the NSA and the telecom…
61 min
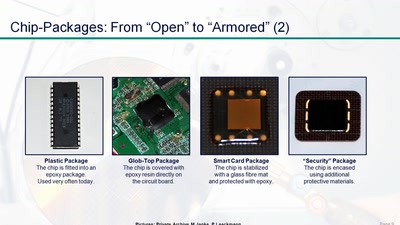
Uncaging Microchips
Techniques for Chip Preparation

60 min
From Computation to Consciousness
How computation helps to explain mind, universe and…
60 min
Why is GPG "damn near unusable"?
An overview of usable security research
58 min
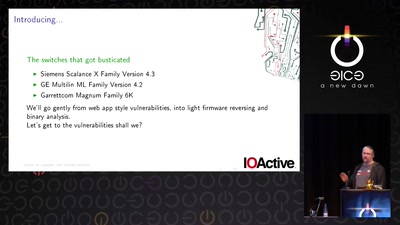
Switches Get Stitches
Industrial System Ownership
61 min
Rocket Kitten: Advanced Off-the-Shelf Targeted Attacks Against Nation States
A Deep Technical Analysis
63 min