Search for "Olga" returned 131 results
62 min
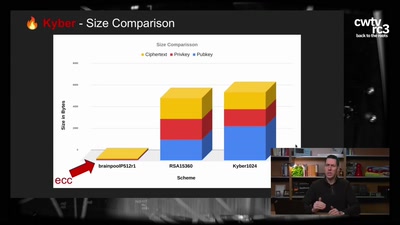
Kyber and Post-Quantum Crypto
How does it work?
53 min
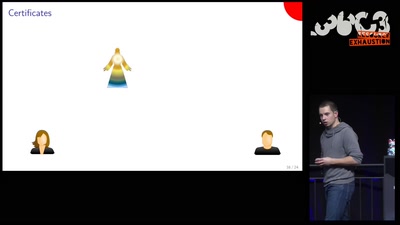
Cryptography demystified
An introduction without maths

46 min
SELECT code_execution FROM * USING SQLite;
--Gaining code execution using a malicious SQLite database

37 min
Hacking (with) a TPM
Don't ask what you can do for TPMs, Ask what TPMs can do…
44 min
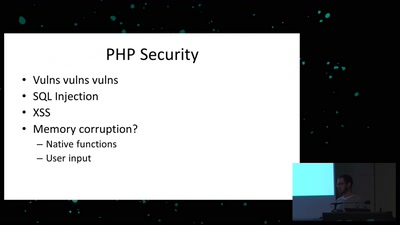
Exploiting PHP7 unserialize
teaching a new dog old tricks
58 min
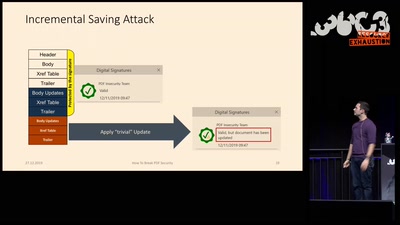
How to Break PDFs
Breaking PDF Encryption and PDF Signatures
36 min
A Blockchain Picture Book
Blockchain origins and related buzzwords, described in…
29 min
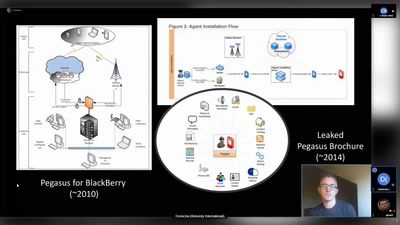
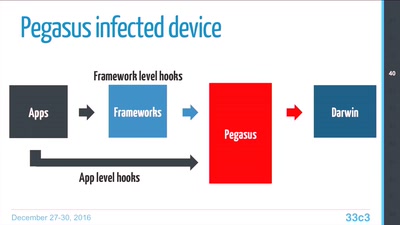
Pegasus internals
Technical Teardown of the Pegasus malware and Trident…
32 min
The Case for Scale in Cyber Security
Security Track Keynote

56 min
Wer liegt hier wem auf der Tasche?
Genug mit dem Bürgergeld-Fetisch. Stürmt die Paläste!
32 min
Von Alpakas, Hasenbären und Einhörnern – Über Anerkennungskultur
Wie Wertschätzung in (Tech-)Communities gelingen kann
44 min
What the cyberoptimists got wrong - and what to do about it
Tech unexeptionalism and the monopolization of every…

63 min
The Case Against WikiLeaks: a direct threat to our community
How to understand this historic challenge and what we can…

32 min