Search for "Sven Brauch" returned 200 results

72 min
Console Hacking
Breaking the 3DS

37 min
Hacking (with) a TPM
Don't ask what you can do for TPMs, Ask what TPMs can do…
59 min
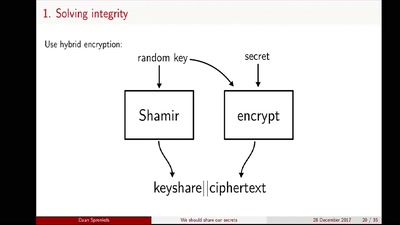
We should share our secrets
Shamir secret sharing: How it works and how to implement it
60 min
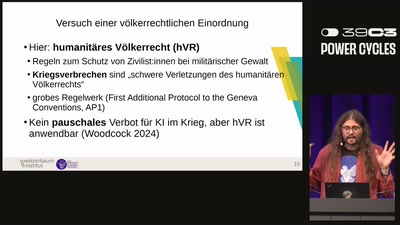
Programmierte Kriegsverbrechen?
Über KI-Systeme im Kriegseinsatz in Gaza und warum…
40 min
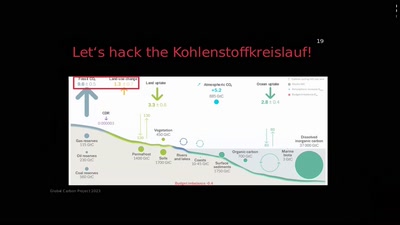
Hacking the Climate
Mit Climate Engineering raus aus der Klimakrise?
59 min
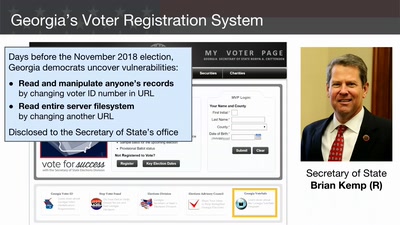
Election Cybersecurity Progress Report
Will the U.S. be ready for 2020?
60 min
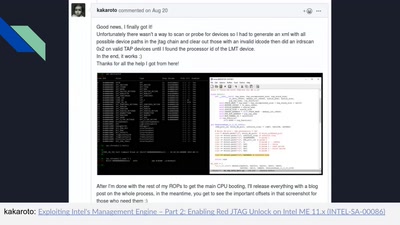
Intel Management Engine deep dive
Understanding the ME at the OS and hardware level
58 min
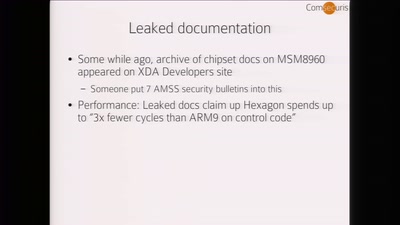
Baseband Exploitation in 2013
Hexagon challenges
57 min
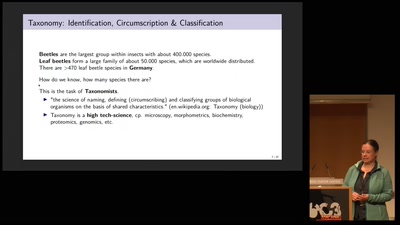
Protecting the Wild
Conservation Genomics between Taxonomy, Big Data,…
33 min
Turing Complete User
What can be done to protect the term, the notion and the…
58 min
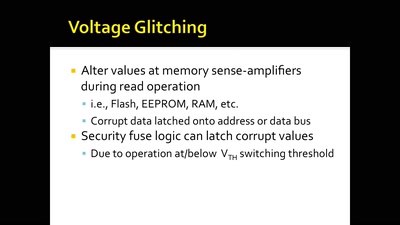
Glitching For n00bs
A Journey to Coax Out Chips' Inner Secrets

58 min
Funkzellenabfrage: Die alltägliche Rasterfahndung unserer Handydaten
Wie wir alle regelmäßig den Behörden ins Netz gehen und wie…

61 min
Deploying TLS 1.3: the great, the good and the bad
Improving the encrypted the web, one round-trip at a time
56 min
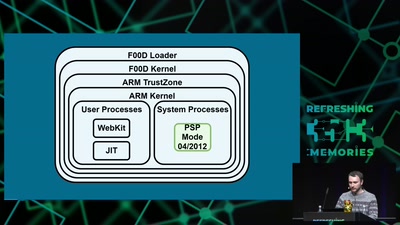
Viva la Vita Vida
Hacking the most secure handheld console
120 min
Hacken, dass...?
Ack, die Wette gilt!
65 min