Search for "sECuRE" returned 800 results
29 min
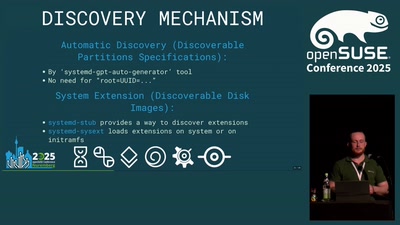
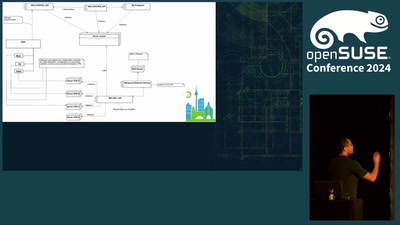
The Unified Kernel Image in openSUSE distribution
How to secure the initramfs
47 min
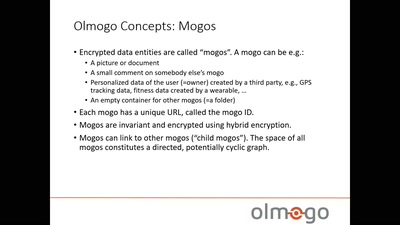
Olmogo - because it's your data!
A cryptographically secure social network platform
60 min
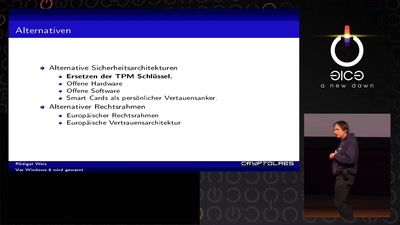
Vor Windows 8 wird gewarnt
Und nichts (Secure) Bootet mehr?
30 min
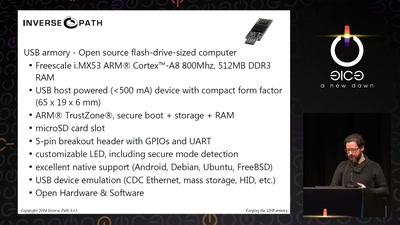
Forging the USB armory
Creating an open source secure flash-drive-sized computer
55 min
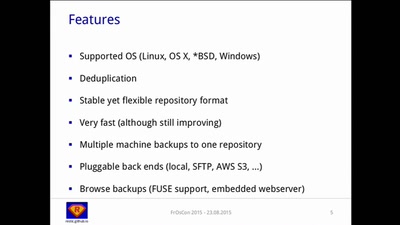
A Solution to the Backup Inconvenience
Fast, Secure and Efficient Backups with "restic"
56 min
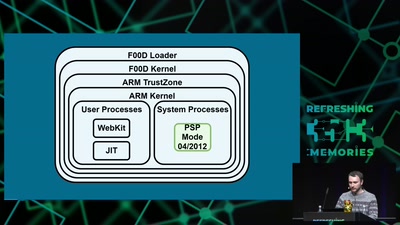
Viva la Vita Vida
Hacking the most secure handheld console
63 min
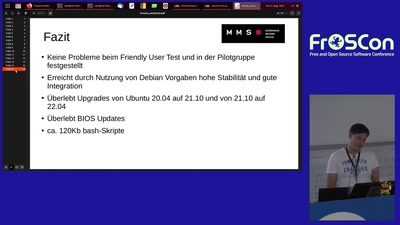
sectpmctl für LUKS Full Disk Encryption (FDE)
Secure Boot und TPM gestützte LUKS…

10 min
Certificate Auto Enrollment on Linux: A Practical Guide
Empowering Secure Connectivity with Samba's Certificate…
69 min
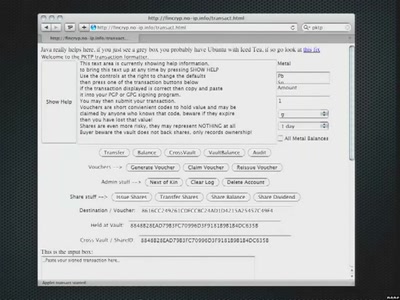
Financing The Revolution
Secure, private value transactions using digital cash
49 min
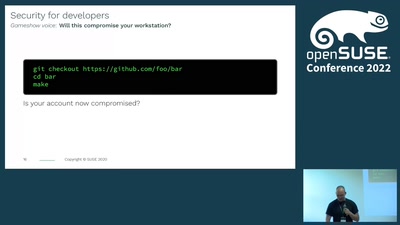
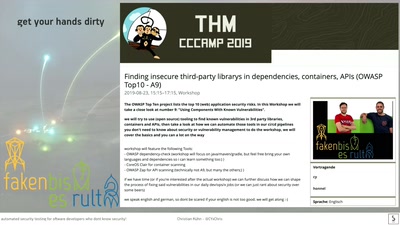
Automated security testing for Software Developers who dont know security!
secure your apps and servers through continuous integration
15 min
Midori is much more than a web browser
Midori is a light, fast and secure web browser that…
61 min
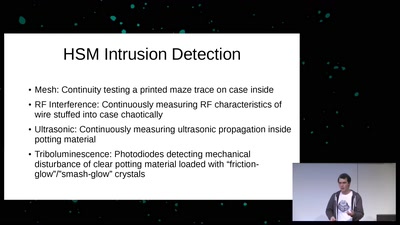
Untrusting the CPU
A proposal for secure computing in an age where we cannot…

63 min
Web-App-Encryption
Is your data secure by default? How Django can be used to…
46 min
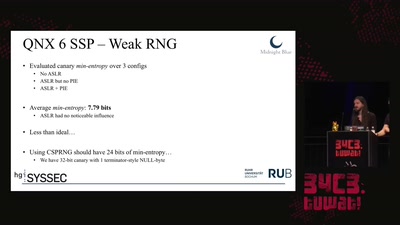
Taking a scalpel to QNX
Analyzing & Breaking Exploit Mitigations and Secure Random…

32 min
Cryptokids
empower kids and provide tools for them to be more secure…
59 min
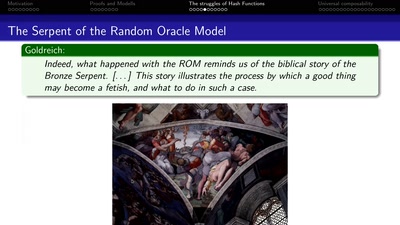
Provable Security
How I learned to stop worrying and love the backdoor

62 min