Search for "glow" returned 1383 results

61 min
Deploying TLS 1.3: the great, the good and the bad
Improving the encrypted the web, one round-trip at a time
29 min
What de.fac2?
Attacking an opensource U2F device in 30 minutes or less
49 min
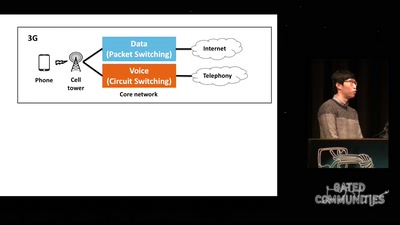
Dissecting VoLTE
Exploiting Free Data Channels and Security Problems

41 min
Extracting keys from FPGAs, OTP Tokens and Door Locks
Side-Channel (and other) Attacks in Practice

39 min
Hacking the Czech Parliament via SMS
A parliamentary drama of 223 actors
47 min
Jailbreaking iOS
From past to present
29 min
Building and Breaking Wireless Security
Wireless Physical Layer Security & More...
59 min
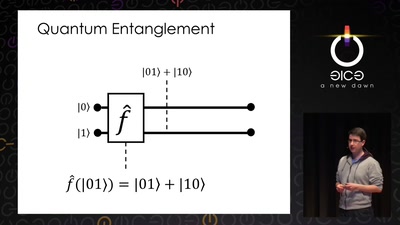
Let's build a quantum computer!
Understanding the architecture of a quantum processor
57 min
The Precariat: A Disruptive Class for Disruptive Times.
Why and How the Precariat will define the Global…
44 min
Replication Prohibited
3D printed key attacks
61 min
Rocket Kitten: Advanced Off-the-Shelf Targeted Attacks Against Nation States
A Deep Technical Analysis

39 min
Hurra, diese Welt geht unter!?
Welche kollektiven Erzählungen brauchen wir, um in der…

58 min
Uncertain Concern
How Undocumented Immigrants in the US Navigate Technology
53 min
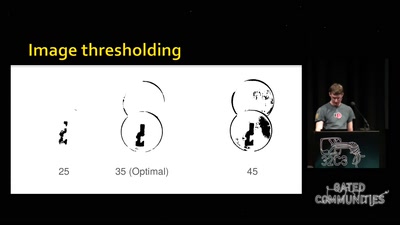
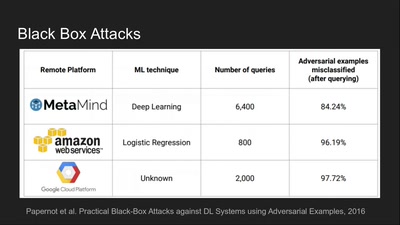
Deep Learning Blindspots
Tools for Fooling the "Black Box"
55 min
YOU’VE JUST BEEN FUCKED BY PSYOPS
UFOS, MAGIC, MIND CONTROL, ELECTRONIC WARFARE, AI, AND THE…

59 min
Security of the IC Backside
The future of IC analysis
95 min
Platform System Interface
Design und Evaluation holistischer Computerarchitektur
58 min