Search for "csk" returned 1372 results
54 min
Tactical Embodiment
Activism and Performance In Hostile Spaces Online
38 min
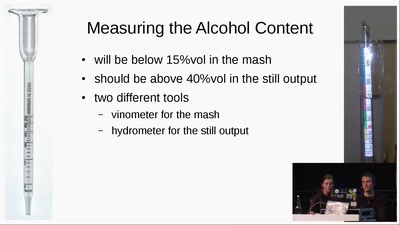
Schnaps Hacking
from apple to schnaps -- a complete diy-toolchain

25 min
»Hard Drive Punch«
Destroying data as a performative act
60 min
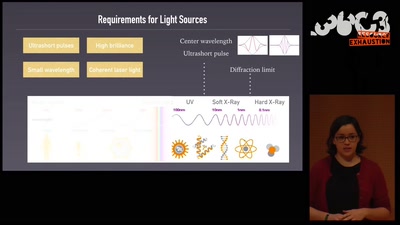
An ultrashort history of ultrafast imaging
Featuring the shortest movies and the largest lasers

63 min
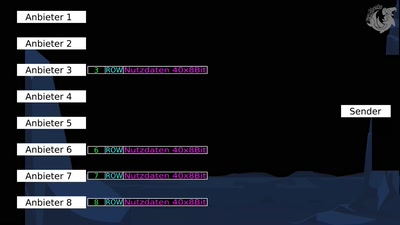
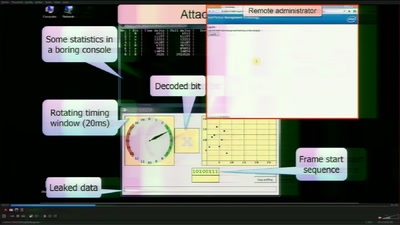
Dissecting HDMI
Developing open, FPGA-based capture hardware for conference…

45 min
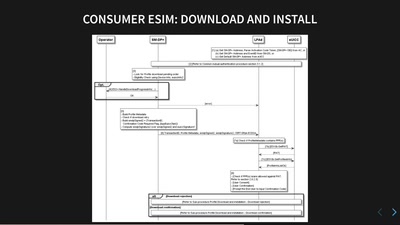
HbbTV Security
OMG - my Smart TV got pr0wn3d
59 min
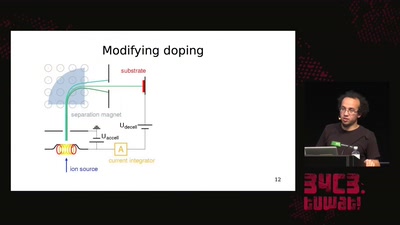
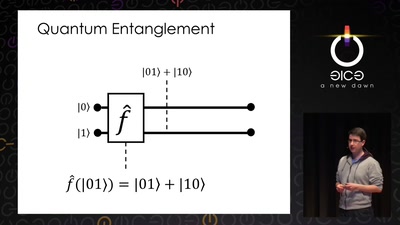
Let's build a quantum computer!
Understanding the architecture of a quantum processor
64 min
We only have one earth
A case for expansionistic space policy
41 min
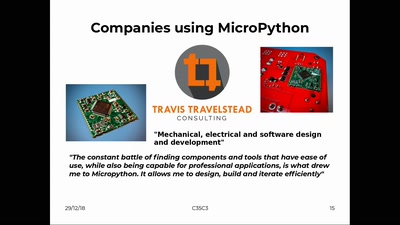
MicroPython – Python for Microcontrollers
How high-level scripting languages make your hardware…
58 min
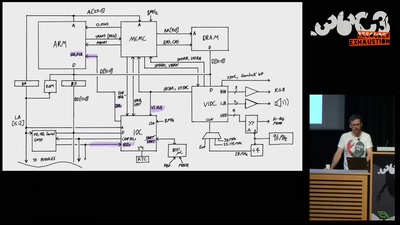
The Ultimate Acorn Archimedes talk
Everything about the Archimedes computer (with zero…
43 min
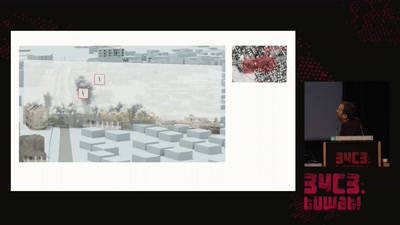
Forensic Architecture
Forensic Architecture is an independent research agency…
58 min
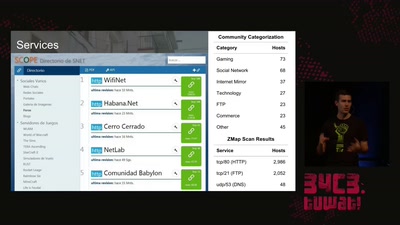
The Internet in Cuba: A Story of Community Resilience
Get a unique tour of some of the world’s most unusual…
61 min
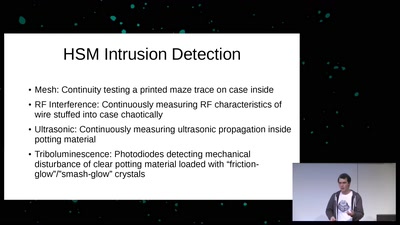
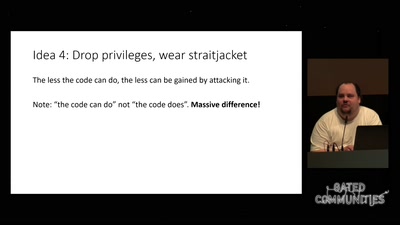
Untrusting the CPU
A proposal for secure computing in an age where we cannot…
60 min