Search for " Leo" returned 1822 results
61 min
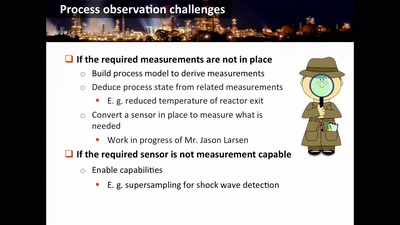
Damn Vulnerable Chemical Process
Exploitation in a new media
65 min
The Untold Story of Edward Snowden’s Escape from Hong Kong
and How You Can Help the Refugees Who Saved His Life
58 min
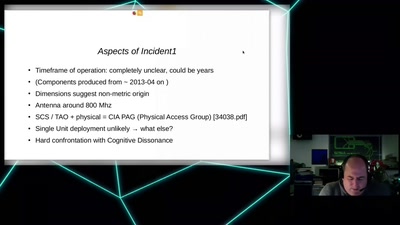
CIA vs. Wikileaks
Intimiditation surveillance and other tactics observed and…
61 min
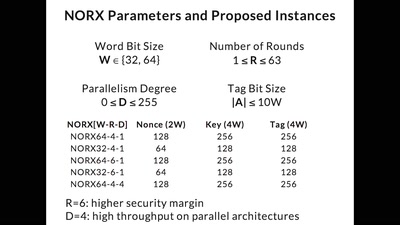
CAESAR and NORX
Developing the Future of Authenticated Encryption

42 min
KI im Klassenzimmer - ein Update!
Wie KI in der Schule wirklich entlasten könnte
61 min
Programming FPGAs with PSHDL
Let's create the Arduino for FPGAs

61 min
Net Neutrality in Europe
alea iacta est
57 min
TrustZone-M(eh): Breaking ARMv8-M's security
Hardware attacks on the latest generation of ARM Cortex-M…
55 min