Search for "simpel" returned 1217 results
49 min
BREACH in Agda
Security notions, proofs and attacks using dependently…
60 min
Lifting the Fog on Red Star OS
A deep dive into the surveillance features of North Korea's…
43 min
No PoC? No Fix! - A sad Story about Bluetooth Security
It is just a broken memcpy in the Bluetooth stack. Do we…
31 min
PUFs, protection, privacy, PRNGs
an overview of physically unclonable functions
60 min
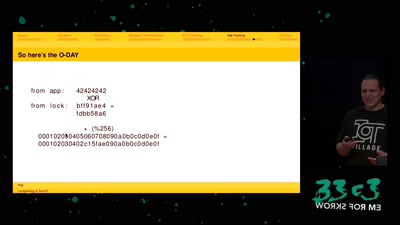
Lockpicking in the IoT
...or why adding BTLE to a device sometimes isn't smart at…
55 min
Cat & Mouse: Evading the Censors in 2018
Preserving access to the open Internet with circumvention…
60 min
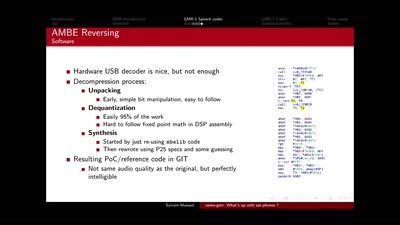
osmo-gmr: What's up with sat-phones ?
Piecing together the missing bits
46 min
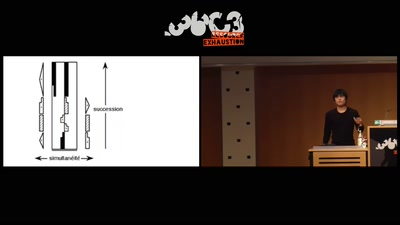
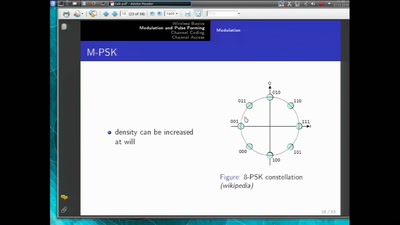
Basics of Digital Wireless Communication
introduction to software radio principles
66 min
31C3 Keynote
A New Dawn
30 min
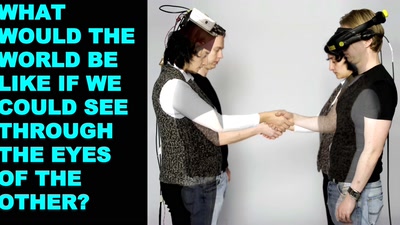
The Machine To Be Another
Exploring identity and empathy through neuroscience,…

62 min
To Protect And Infect, Part 2
The militarization of the Internet
58 min
Confessions of a future terrorist
A rough guide to over-regulating free speech with…
58 min
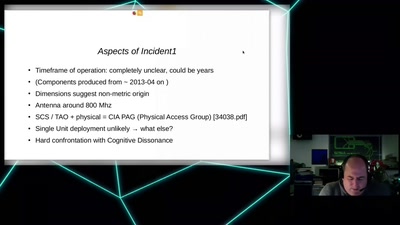
CIA vs. Wikileaks
Intimiditation surveillance and other tactics observed and…
60 min