Search for " Leo" returned 1822 results
55 min
Cat & Mouse: Evading the Censors in 2018
Preserving access to the open Internet with circumvention…
19 min
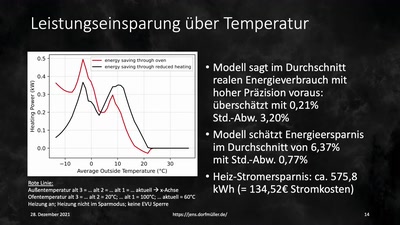
Fooled by the Website Carbon Calculator
Green Coding & Measuring the Environmental Impacts of IT
48 min
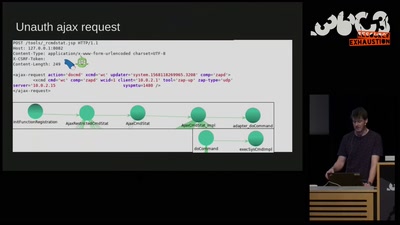
Don't Ruck Us Too Hard - Owning Ruckus AP Devices
3 different RCE vulnerabilities on Ruckus Wireless access…
44 min
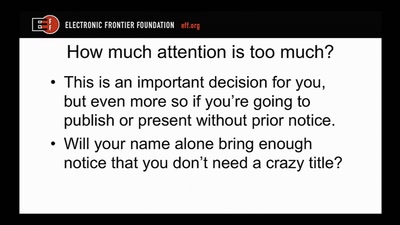
Disclosure DOs, Disclosure DON'Ts
Pragmatic Advice for Security Researchers
21 min
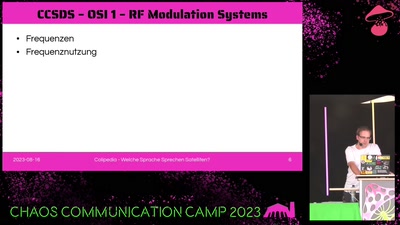
Welche Sprache sprechen Satelliten?
Ein Überblick über Protokolle und verwendete…

45 min
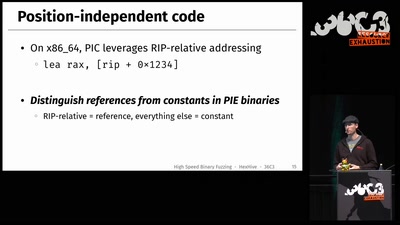
Triggering Deep Vulnerabilities Using Symbolic Execution
Deep program analysis without the headache
61 min
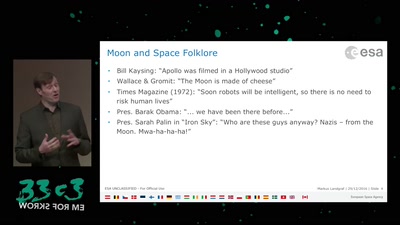
An Elevator to the Moon (and back)
Space Transportation and the Extraterrestrial Imperative

45 min
A geometry engine from first principles
the first three years of a six month project.
61 min
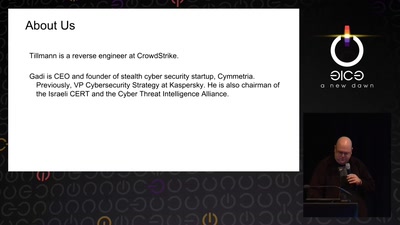
Rocket Kitten: Advanced Off-the-Shelf Targeted Attacks Against Nation States
A Deep Technical Analysis
63 min
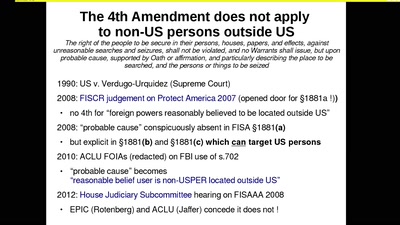
The Cloud Conspiracy 2008-2014
how the EU was hypnotised that the NSA did not exist
58 min
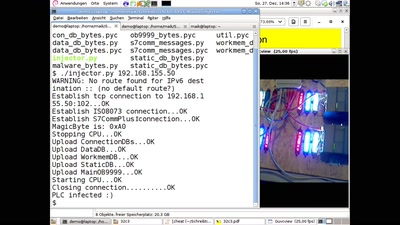
PLC-Blaster
Ein Computerwurm für PLCs
47 min
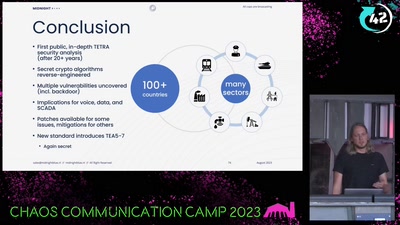
All cops are broadcasting
Obtaining the secret TETRA primitives after decades in the…
39 min
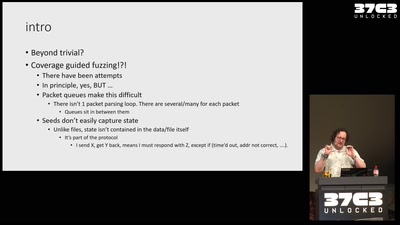
Fuzzing the TCP/IP stack
beyond the trivial
60 min