Search for "cbass" returned 400 results

9 min
Präsentation „Automatisierungs-Demystifizierungs-Diskurs-Maschine“
Impuls von Dr. Stefan Ullrich zur partizipativen…
39 min
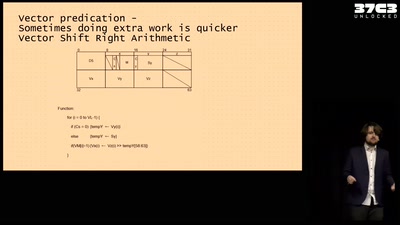
Making homebrew for your very own Vector Super Computer
Adventures running a NEC Vector Engine for fun and ...…
44 min
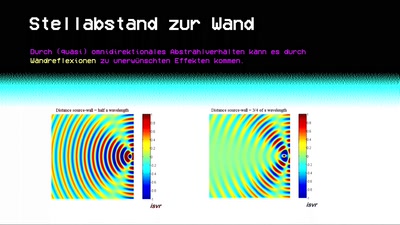
Sonic Alchemy
Mehr als nur Lärm: Ein Sprint vom kleinen Audio-Einmaleins…
60 min
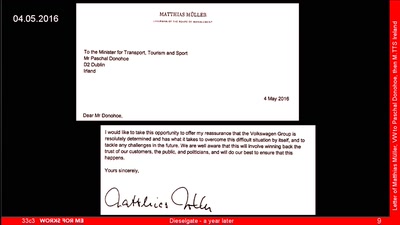
Dieselgate – A year later
env stinks || exit
47 min
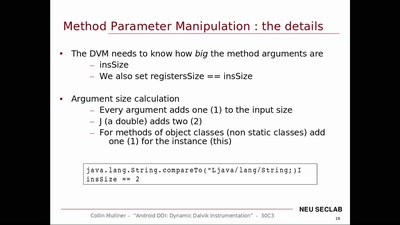
Android DDI
Dynamic Dalvik Instrumentation of Android Applications and…
59 min
How to teach programming to your loved ones
Enabling students over example-driven teaching
51 min
Ecuador: how an authoritarian government is fooling the entire world
Guess what? The Government of Rafael Correa actually is…

40 min
Auf die Dauer hilft nur Power
Herausforderungen für dezentrale Netzwerke aus Sicht der…
59 min
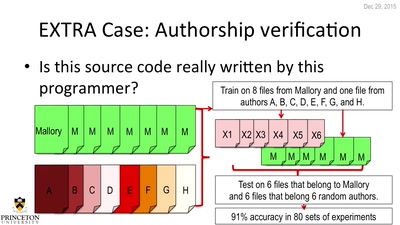
De-anonymizing Programmers
Large Scale Authorship Attribution from Executable Binaries…
60 min
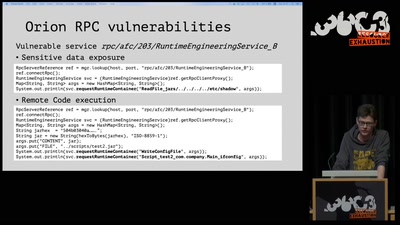
On the insecure nature of turbine control systems in power generation
A security study of turbine control systems in power…
42 min