Search for "sECuRE" returned 800 results
57 min
TrustZone-M(eh): Breaking ARMv8-M's security
Hardware attacks on the latest generation of ARM Cortex-M…
28 min
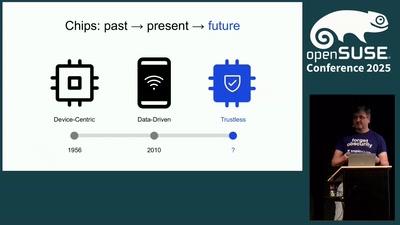
Open Source is no longer just for software:
Why the community needs open source hardware to ensure…
69 min
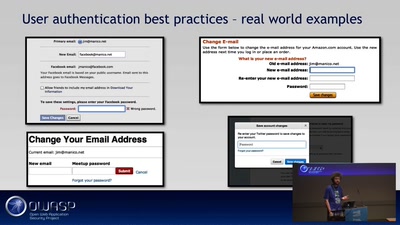
OWASP ProActive Controls
Sichere Anwendungen erstellen?
60 min
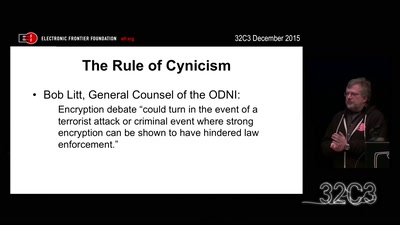
Crypto Wars Part II
The Empires Strike Back
61 min
Certificate Authority Collapse
Will the EU Succeed in Regulating HTTPS?
36 min
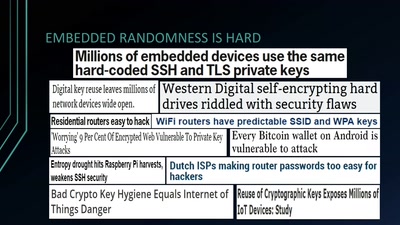
Wheel of Fortune
Analyzing Embedded OS Random Number Generators
60 min
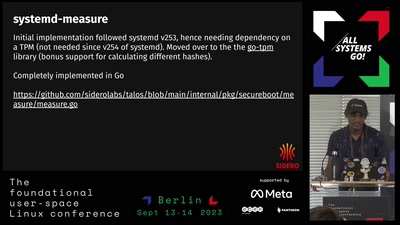
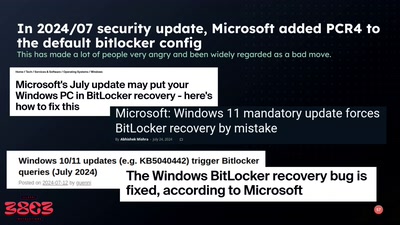
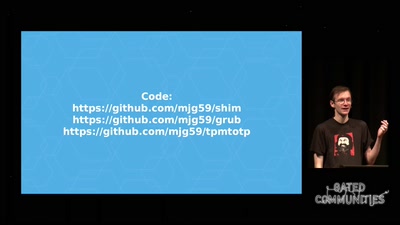
Beyond Anti Evil Maid
Making it easier to avoid low-level compromise, and why…
43 min
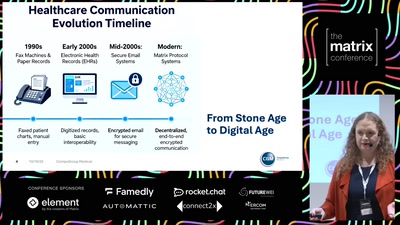
Matrix as a Bridge
Enabling Cross-Border Healthcare Communication Through Open…
51 min
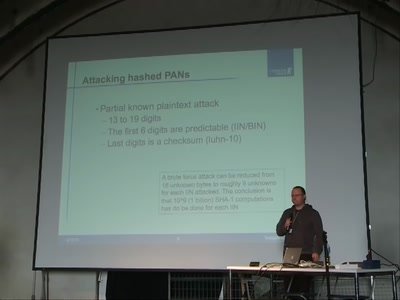
Strong encryption of credit card information
Attacks on common failures when encrypting credit card…
54 min
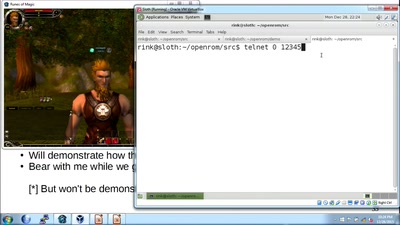
How hackers grind an MMORPG: by taking it apart!
An introduction to reverse engineering network protocols

59 min
Security of the IC Backside
The future of IC analysis
56 min