Search for "Ben" returned 9332 results

42 min
Just in Time compilers - breaking a VM
Practical VM exploiting based on CACAO
53 min
Privaterra - Report from the field
IT Security and Human Rights organizations - The needs, the…

59 min
e-Voting: The silent decline of public control
Why German voting machines do not meet the requirements of…
45 min
Hopalong Casualty
On automated video analysis of human behaviour
26 min
Don't scan, just ask
A new approach of identifying vulnerable web applications
61 min
Certificate Authority Collapse
Will the EU Succeed in Regulating HTTPS?

57 min
7 years, 400+ podcasts, and a whole lot of Frequent Flyer Miles
Lessons learned from producing a weekly independent podcast…
60 min
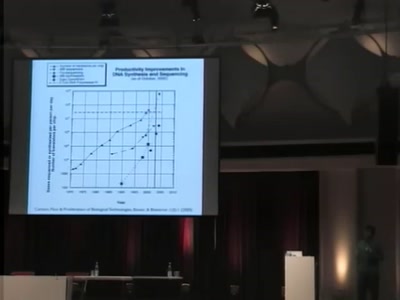
Programming DNA
A 2-bit language for engineering biology

95 min
Analysis of a strong Random Number Generator
by anatomizing Linux' CPRNG
55 min
Our daily job: hacking the law
The key elements of policy hacking
25 min
SIP home gateways under fire
Source routing attacks applied to SIP
56 min
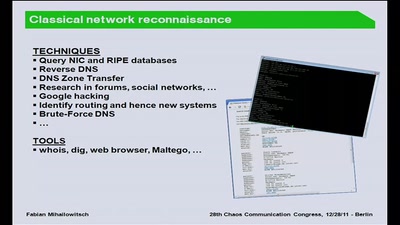
Corp vs. Corp
Profiling Modern Espionage
64 min
What is in a name?
Identity-Regimes from 1500 to the 2000s
52 min
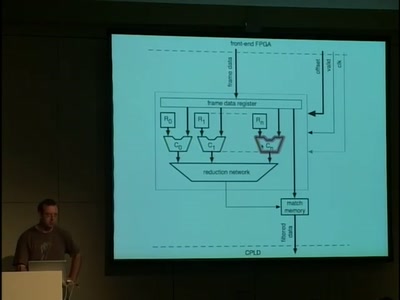
A 10GE monitoring system
Hacking a 10 Gigabit Intrusion detection and prevention…
48 min
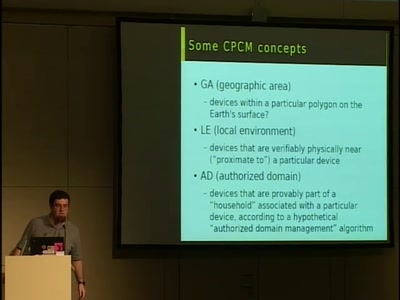
DRM comes to European digital TV
How the DVB project is locking down TV standards and…
62 min
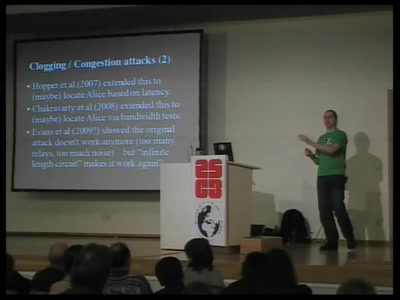
Security and anonymity vulnerabilities in Tor
Past, present, and future
56 min
Rootkits in your Web application
Achieving a permanent stealthy compromise of user accounts…
47 min
WIPO Broadcasting Treaty
Lobbying on an International Scale

60 min
Data Retention and PNR
The Brussels Workshop

59 min
10GE monitoring live!
How to find that special one out of millions
63 min