Search for "Leah" returned 1493 results
38 min
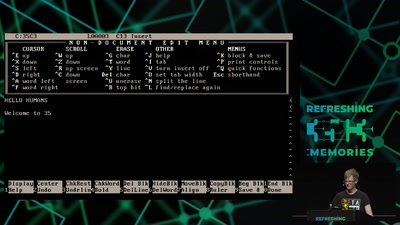
A deep dive into the world of DOS viruses
Explaining in detail just how those little COM files…
59 min
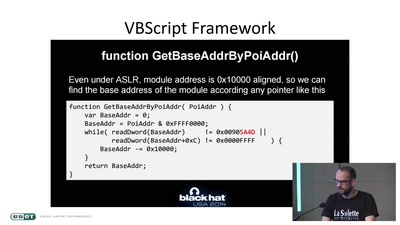
Visiting The Bear Den
A Journey in the Land of (Cyber-)Espionage
26 min
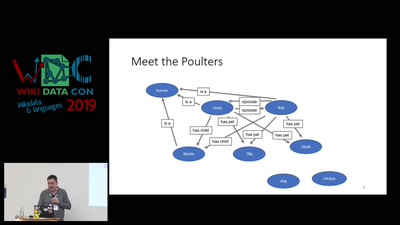
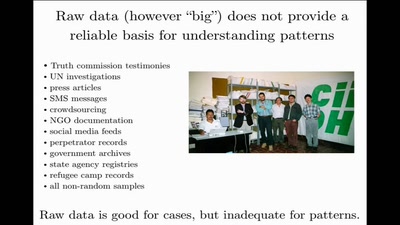
Data Mining for Good
Using random sampling, entity resolution, communications…
57 min
Du kannst alles hacken – du darfst dich nur nicht erwischen lassen.
OpSec für Datenreisende
32 min
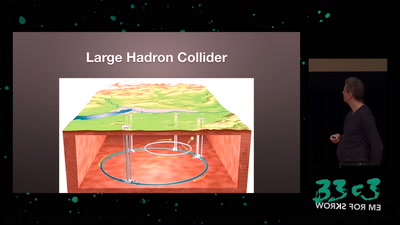
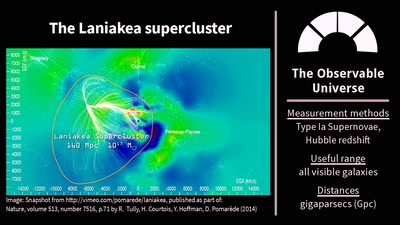
The Universe Is, Like, Seriously Huge
Stuff in Space Is Far Away – but How Do We Know?

31 min
Sysadmins of the world, unite!
a call to resistance
59 min
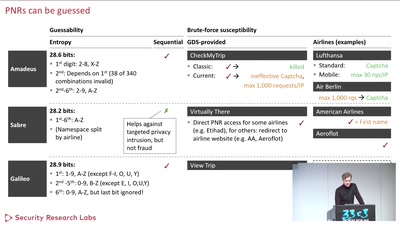
Where in the World Is Carmen Sandiego?
Becoming a secret travel agent
56 min
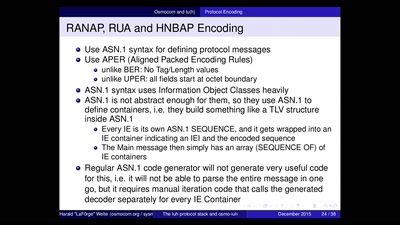
Running your own 3G/3.5G network
OpenBSC reloaded
56 min
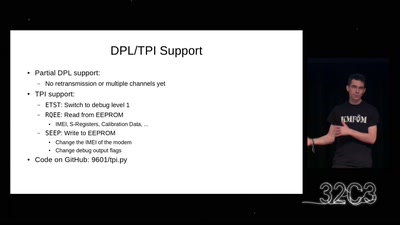
Iridium Update
more than just pagers

33 min
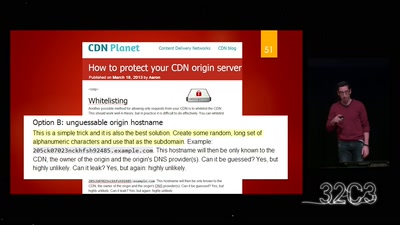
Gone in 60 Milliseconds
Intrusion and Exfiltration in Server-less Architectures
44 min
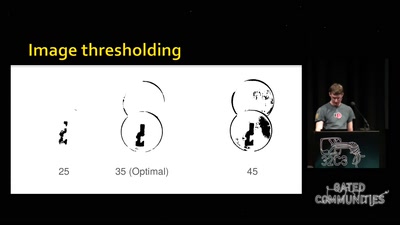
Replication Prohibited
3D printed key attacks
60 min
Check your privileges!
How to drop more of your privileges to reduce attack…
60 min
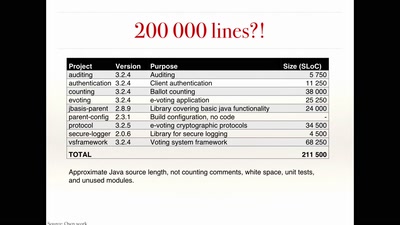
The rise and fall of Internet voting in Norway
Evaluating a complex cryptographic implementation

32 min
Finding the Weak Crypto Needle in a Byte Haystack
Automatic detection of key-reuse vulnerabilities

42 min
Citzens or subjects? The battle to control our bodies, speech and communications
A call to action to defend our ePrivacy and eliminate…
55 min