Search for "Jon" returned 9599 results
59 min
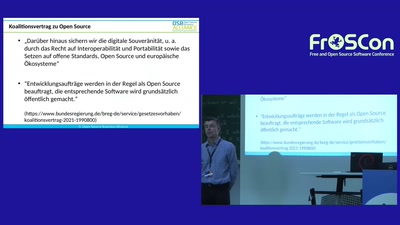
Routerzwang und Funkabschottung – Was Aktivisten davon lernen können
Von Erfolgen und Fehlern lernen und auf das eigene Anliegen…
37 min
Self-documenting computation
What is the best way to present programs to non-programmers?
31 min
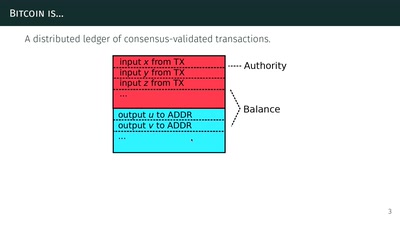
The Zcash anonymous cryptocurrency
or zero-knowledge succinct non-interactive arguments of…

85 min
Stream: Security Nightmares
in english!!11oneeleven (translated on the fly)
30 min
The philosophy of hacking
Contemplations on the essence of hacking and its…
46 min
Neuschreiben nicht empfohlen
Warum man eine bereits existierende Applikation nicht von…

41 min
Chaos Communication Chemistry
DNA security systems based on molecular randomness
22 min
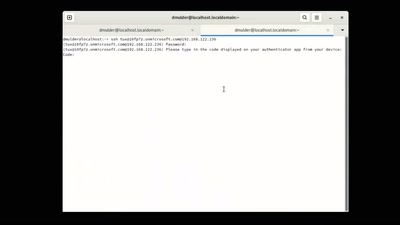
Bridging Worlds: Linux and Azure AD
Azure Entra ID and Intune on Linux
56 min
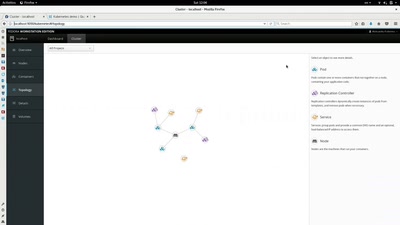
Introduction to container orchestration with Kubernetes
Everything you need to know for your next job interview
30 min
All Our Shared Spectrum Are Belong to Us
Visualizing WLAN Channel Usage on OpenWRT
47 min
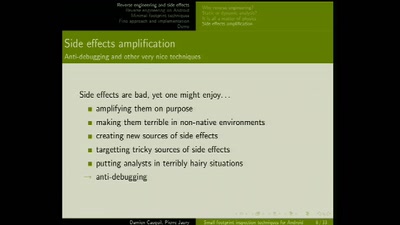
Small footprint inspection techniques for Android
Reverse engineering on Android platforms
38 min
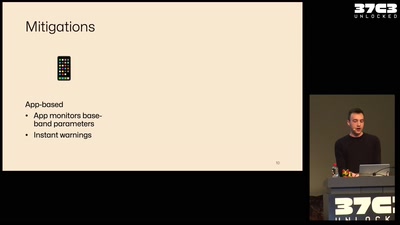
What your phone won’t tell you
Uncovering fake base stations on iOS devices
53 min
Moving towards fully encrypted web
Checkpoint on the road towards inevitable
48 min
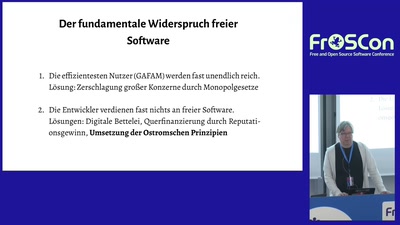
Die Tragik der Software-Allmende
Freie Software und die acht Designprinzipien für Commons…
40 min
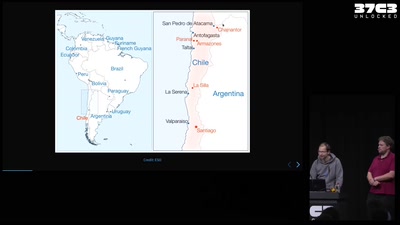
The Extremely Large Telescope (ELT)
Building the biggest optical telescope on earth
57 min
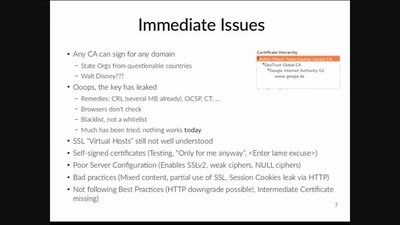
To Make Hearts Bleed
A Native Developer's Account On SSL

42 min
Just in Time compilers - breaking a VM
Practical VM exploiting based on CACAO
46 min
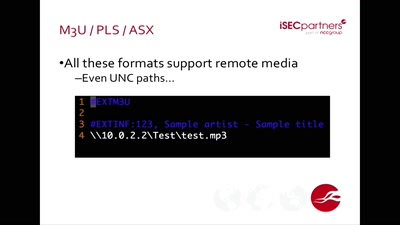
Bugged Files
Is Your Document Telling on You?
83 min
SDR - Fluch, Segen, Möglichkeiten
Der Einsatz von SDR-Technik aus Sicht des Technikers,…

9 min
Präsentation „Automatisierungs-Demystifizierungs-Diskurs-Maschine“
Impuls von Dr. Stefan Ullrich zur partizipativen…
56 min
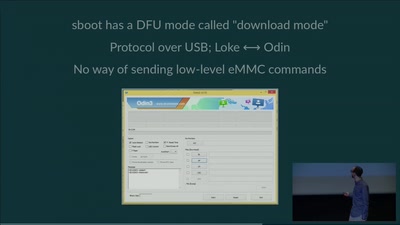
eMMC hacking, or: how I fixed long-dead Galaxy S3 phones
A journey on how to fix broken proprietary hardware by…
58 min