Search for "Ute Holl" returned 1438 results
60 min
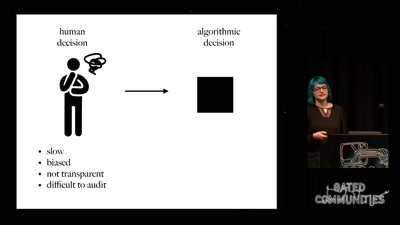
Prediction and Control
Watching Algorithms
51 min
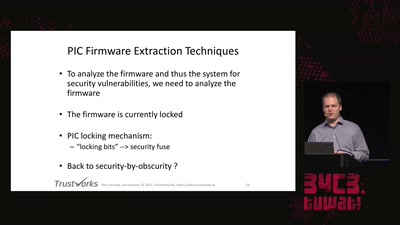
Uncovering vulnerabilities in Hoermann BiSecur
An AES encrypted radio system
58 min
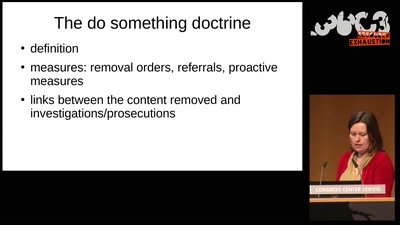
Confessions of a future terrorist
A rough guide to over-regulating free speech with…

42 min
Union Busting
What is it and why you should care
67 min
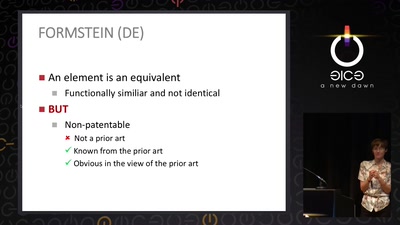
The Maker movement meets patent law
How many windows are open in the patent fortress
55 min
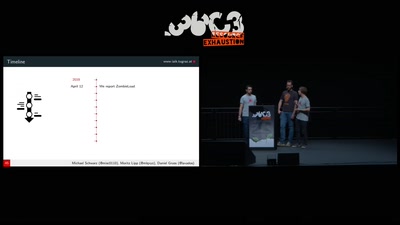
ZombieLoad Attack
Leaking Your Recent Memory Operations on Intel CPUs
65 min
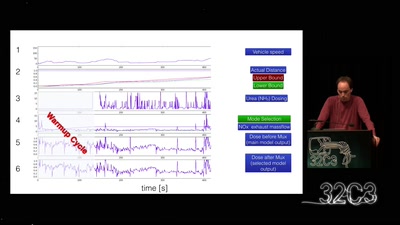
The exhaust emissions scandal („Dieselgate“)
Take a deep breath into pollution trickery
59 min
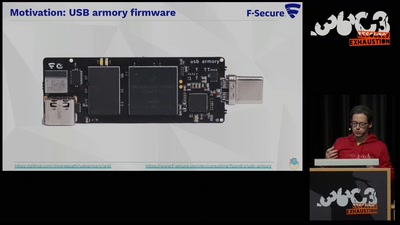
TamaGo - bare metal Go framework for ARM SoCs.
Reducing the attack surface with pure embedded Go.

62 min
HUMUS sapiens
Open Soil Research
40 min
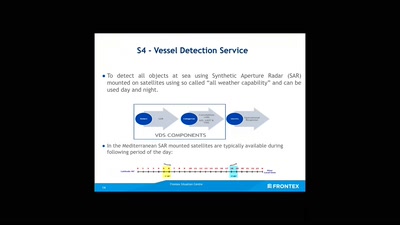
No roborders, no nation, or: smile for a European surveillance propagation
How an agency implements Fortress Europe by degrading…
59 min
Visiting The Bear Den
A Journey in the Land of (Cyber-)Espionage
60 min
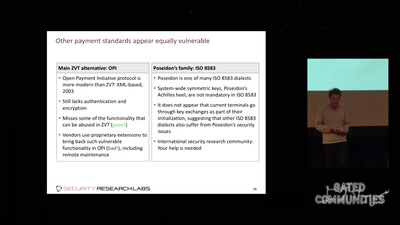
Shopshifting
The potential for payment system abuse

62 min
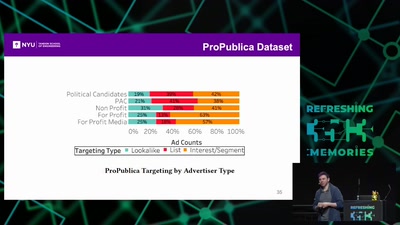
Corporate surveillance, digital tracking, big data & privacy
How thousands of companies are profiling, categorizing,…
59 min
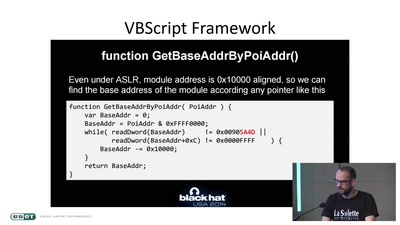
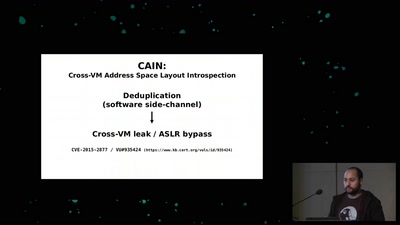
Memory Deduplication: The Curse that Keeps on Giving
A tale of 3 different memory deduplication based…
59 min
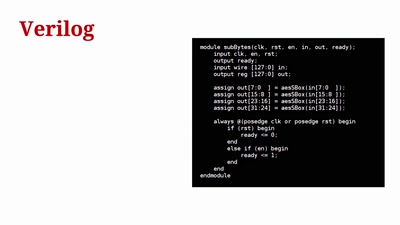
Towards General Purpose Reconfigurable Computing on Novena
FPGAs for Everybody with Novena

61 min
Net Neutrality in Europe
alea iacta est
62 min