Search for "Ute Holl" returned 1438 results
62 min
Calafou, postcapitalist ecoindustrial community
Building a space for grassroots sustainable technology…

51 min
Funky File Formats
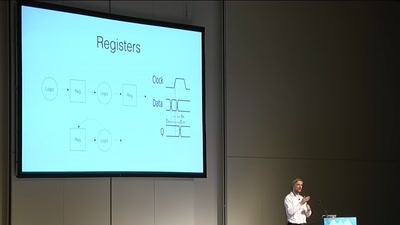
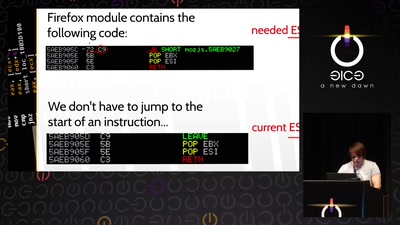
Advanced binary tricks
60 min
Lets break modern binary code obfuscation
A semantics based approach
58 min
How risky is the software you use?
CITL: Quantitative, Comparable Software Risk Reporting

58 min
Cyber all the Wassenaars
Export controls and exploit regulations: braindead and…

32 min
Finding the Weak Crypto Needle in a Byte Haystack
Automatic detection of key-reuse vulnerabilities
72 min
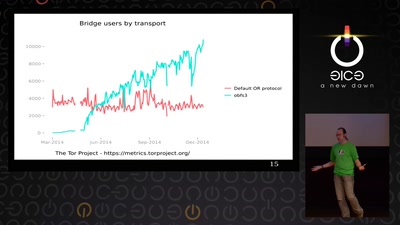
State of the Onion
Neuland

55 min
The Gospel of IRMA
Attribute Based Credentials in Practice

61 min
Trustworthy secure modular operating system engineering
fun(ctional) operating system and security protocol…
55 min
Attribution revolution
Turning copyright upside-down with metadata

46 min
SELECT code_execution FROM * USING SQLite;
--Gaining code execution using a malicious SQLite database
63 min
goto fail;
exploring two decades of transport layer insecurity
58 min
Wie klimafreundlich ist Software?
Einblicke in die Forschung und Ausblick in die…
58 min
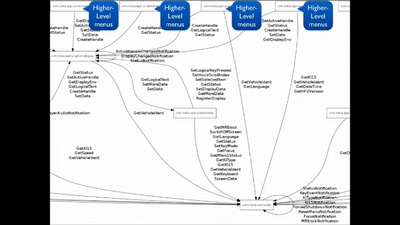
Script Your Car!
Using existing hardware platforms to integrate python into…
58 min
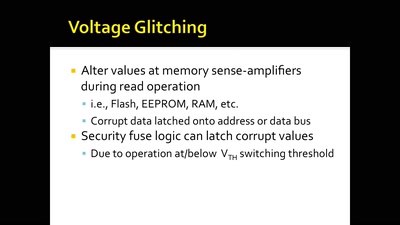
Glitching For n00bs
A Journey to Coax Out Chips' Inner Secrets
64 min