Search for "xif" returned 2079 results

32 min
Finding the Weak Crypto Needle in a Byte Haystack
Automatic detection of key-reuse vulnerabilities

60 min
HAL - The Open-Source Hardware Analyzer
A dive into the foundations of hardware reverse engineering…
60 min
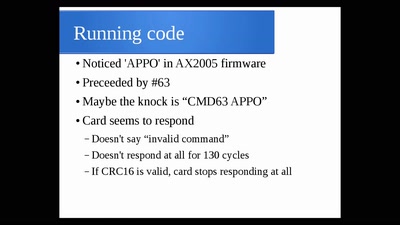
The Exploration and Exploitation of an SD Memory Card
by xobs & bunnie
60 min
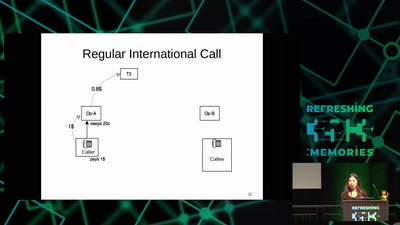
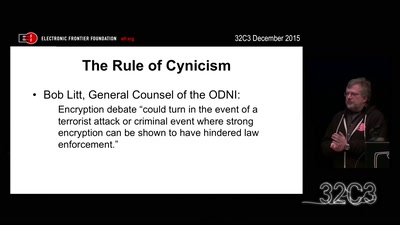
Crypto Wars Part II
The Empires Strike Back
67 min
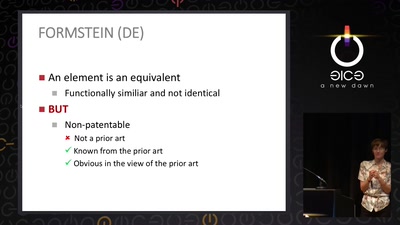
The Maker movement meets patent law
How many windows are open in the patent fortress

37 min
The foodsaving grassroots movement
How cooperative online structures can facilitate…
31 min
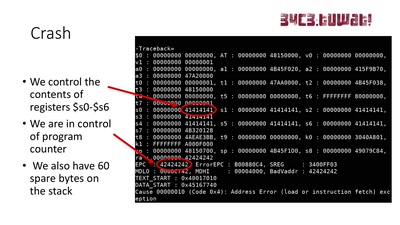
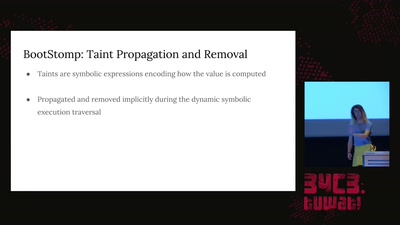
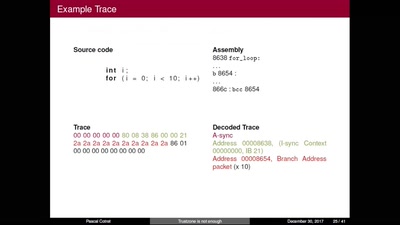
TrustZone is not enough
Hijacking debug components for embedded security
46 min
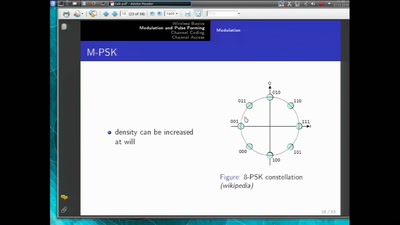
Basics of Digital Wireless Communication
introduction to software radio principles
61 min
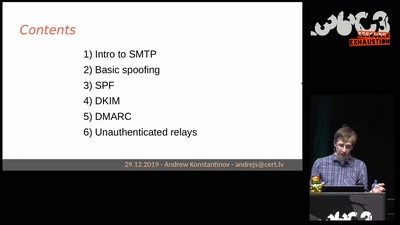
Email authentication for penetration testers
When SPF is not enough
32 min
Technology and Mass Atrocity Prevention
Overview on Current Efforts - We Need Moar H4x0rs?!
60 min
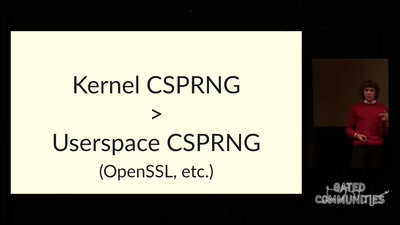
The plain simple reality of entropy
Or how I learned to stop worrying and love urandom
39 min