Search for "Sven" returned 2173 results
55 min
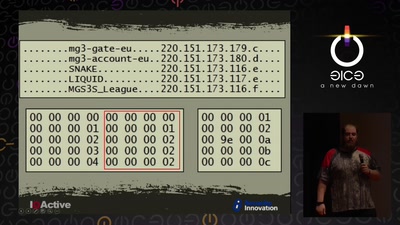
Cyber Necromancy
Reverse Engineering Dead Protocols
55 min
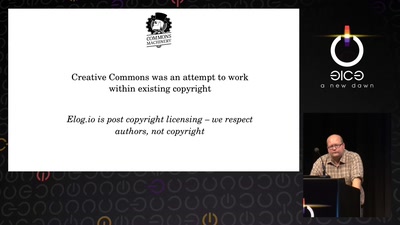
Attribution revolution
Turning copyright upside-down with metadata

42 min
Ecocide and (green) colonialism in Sápmi
Data centers on indigenous land in Northern Europe
57 min
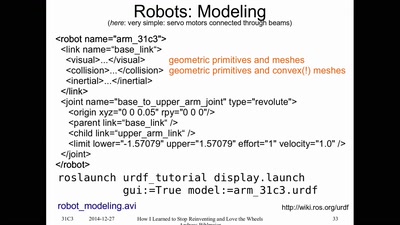
How I Learned to Stop Reinventing and Love the Wheels
or having FUN with (home/hackerspace) robotics
41 min
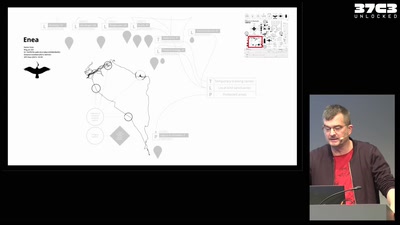
Infrastructure of a migratory bird
Technology and autonomy in more-than-human networks
59 min
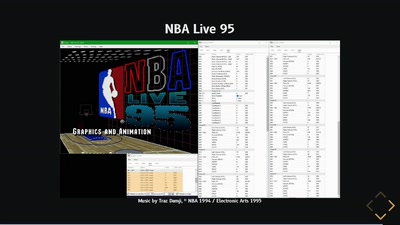
The Ultimate SPC700 Talk
The hardware behind the music of Super Mario World, Chrono…
46 min
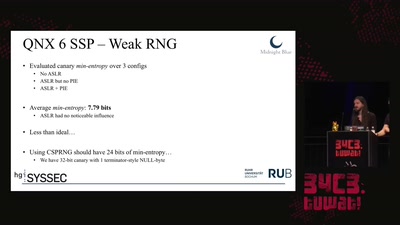
Taking a scalpel to QNX
Analyzing & Breaking Exploit Mitigations and Secure Random…
55 min
Cat & Mouse: Evading the Censors in 2018
Preserving access to the open Internet with circumvention…

46 min
Sendezentrum: Who Killed The Internet?
And a promising alternative for Public Communication and…
59 min
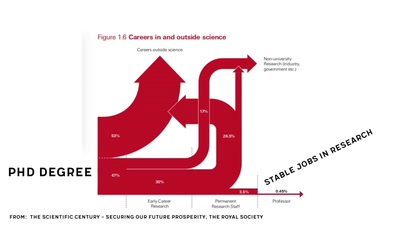
Scientific Literacy 101
Let's understand how the scientific system works

33 min
Global Civil Society Under Attack
Reports from the Frontlines
60 min
Why is GPG "damn near unusable"?
An overview of usable security research

60 min
My Robot Will Crush You With Its Soft Delicate Hands!
How to design and fabricate soft robots using everyday…
59 min
How to teach programming to your loved ones
Enabling students over example-driven teaching
32 min
Technology and Mass Atrocity Prevention
Overview on Current Efforts - We Need Moar H4x0rs?!
30 min
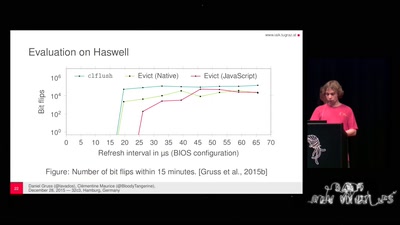
Rowhammer.js: Root privileges for web apps?
A tale of fault attacks on DRAM and attacks on CPU caches

44 min