Search for "olf" returned 7516 results
31 min
Will my hardware work with openSUSE?
Don't be afraid of the kernel
32 min
Think big or care for yourself
On the obstacles to think of emergent technologies in the…
58 min
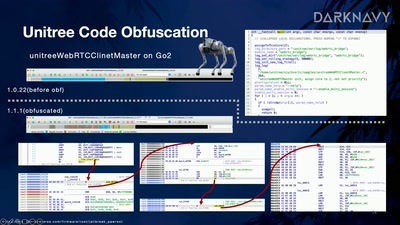
Skynet Starter Kit
From Embodied AI Jailbreak to Remote Takeover of Humanoid…

42 min
Free Software and Platform Regulation
The impact of the Digital Market Act on Free Software
21 min
DevOps for GNOME with Flatpak
And how we improved our contributors experience and…
21 min
Designing PCBs with code
Is designing circuits with code instead of CAD the future…

62 min
Corporate surveillance, digital tracking, big data & privacy
How thousands of companies are profiling, categorizing,…
51 min
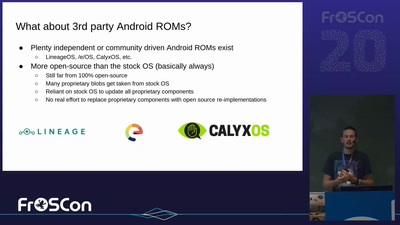
postmarketOS - Digital Independence in Your Pocket
How we can get back control of our phones
30 min
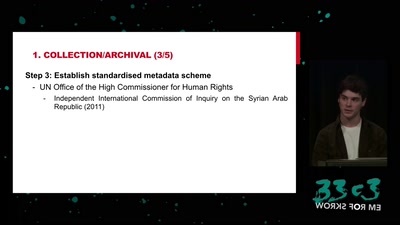
Syrian Archive
Preserving documentation of human rights violations
55 min
Our daily job: hacking the law
The key elements of policy hacking
61 min
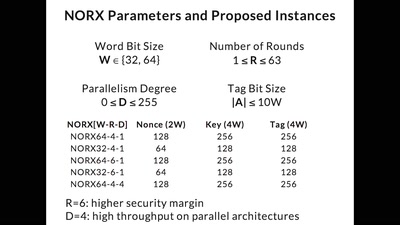
CAESAR and NORX
Developing the Future of Authenticated Encryption
52 min
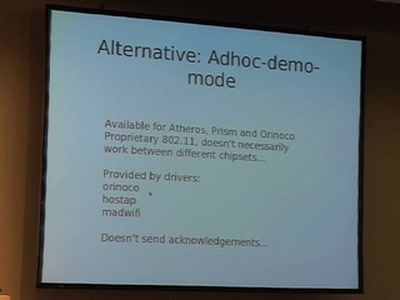
WiFi Long Shots
Wireless connections of 20km and more

58 min
The Infinite Library
Storage and Access of Pornographic Information
31 min
PUFs, protection, privacy, PRNGs
an overview of physically unclonable functions
66 min
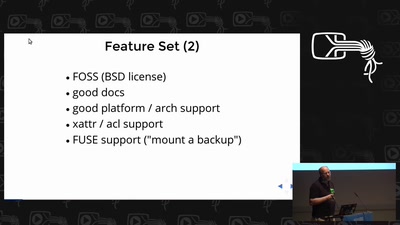
borgbackup
the holy grail of backup software?
40 min
peer to peer communism vs the client-server state
The Political Economy of Network Topologies

47 min
Software Patenting
Adequate means of protection for software.
94 min
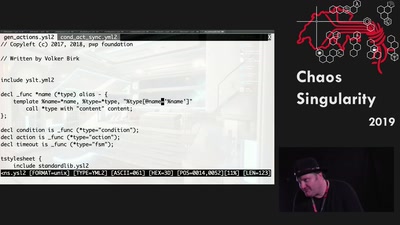
How to generate a network protocol stack
Practical application of writing software generators
30 min