Search for "Apex" returned 180 results
56 min
Running your own 3G/3.5G network
OpenBSC reloaded
55 min
YOU’VE JUST BEEN FUCKED BY PSYOPS
UFOS, MAGIC, MIND CONTROL, ELECTRONIC WARFARE, AI, AND THE…

32 min
Craft, leisure, and end-user innovation
How hacking is conceived in social science research

60 min
From Computation to Consciousness
How computation helps to explain mind, universe and…

45 min
Triggering Deep Vulnerabilities Using Symbolic Execution
Deep program analysis without the headache
41 min
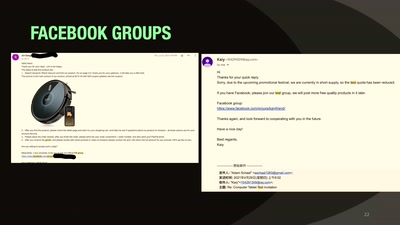
Our Time in a Product Review Cabal
And the malware and backdoors that came with it.
41 min
Why Railway Is Safe But Not Secure
Security Of Railway Communication Protocols
61 min
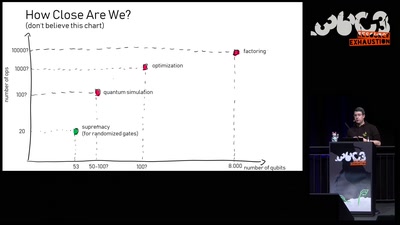
Quantum Computing: Are we there yet?
An introduction to quantum computing and a review of the…
57 min
TrustZone-M(eh): Breaking ARMv8-M's security
Hardware attacks on the latest generation of ARM Cortex-M…
55 min
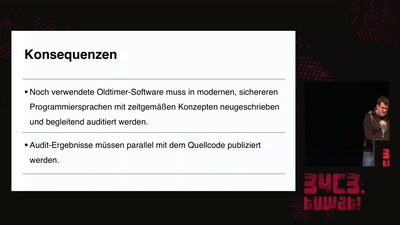
Der PC-Wahl-Hack
Analyse einer Wahlsoftware
63 min
Reconstructing narratives
transparency in the service of justice

55 min
What is Good Technology?
Answers & practical guidelines for engineers.

61 min
QualityLand
Lesung
59 min
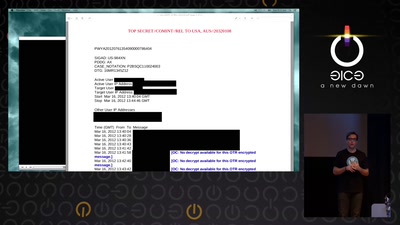
Visiting The Bear Den
A Journey in the Land of (Cyber-)Espionage
58 min
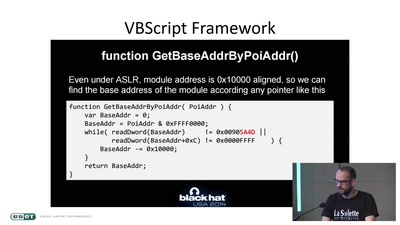
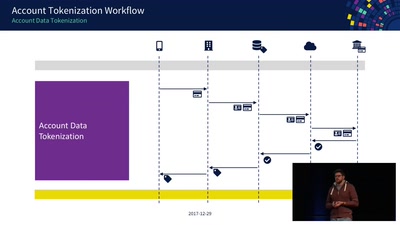
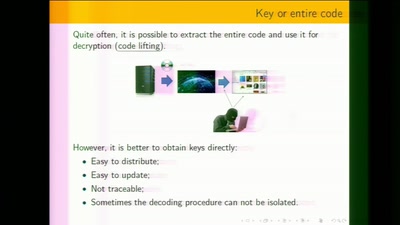
Decoding Contactless (Card) Payments
An Exploration of NFC Transactions and Explanation How…
55 min