Search for "Sven Brauch" returned 200 results
61 min
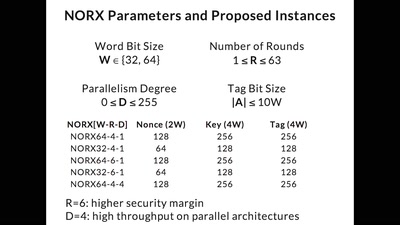
CAESAR and NORX
Developing the Future of Authenticated Encryption
63 min
Kritikalität von Rohstoffen - wann platzt die Bombe?
Ein nicht nuklearer Blick auf das Ende der Welt
31 min
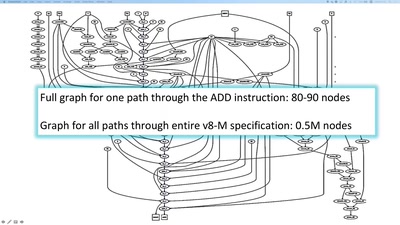
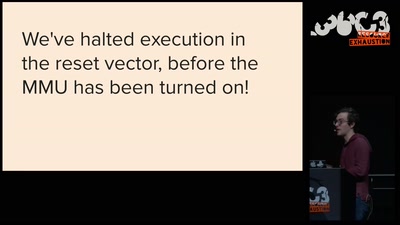
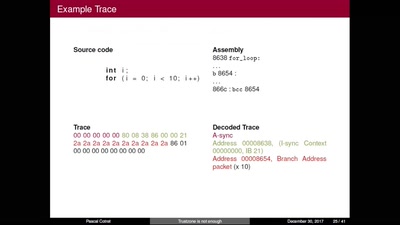
TrustZone is not enough
Hijacking debug components for embedded security

55 min
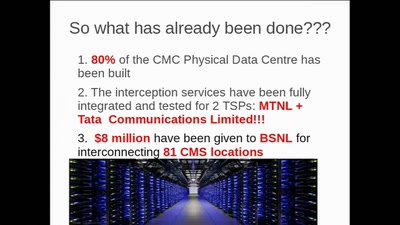
Chatkontrolle
Ctrl+Alt+Delete
42 min
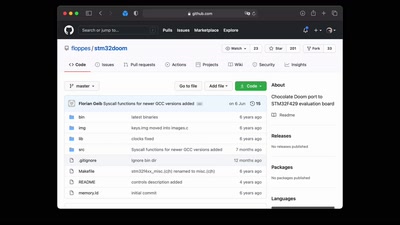
Hacking the Nintendo Game & Watch
Your princess is AES encrypted in another castle
62 min
The Internet (Doesn't) Need Another Security Guide
Creating Internet Privacy and Security Resources That Don't…
54 min
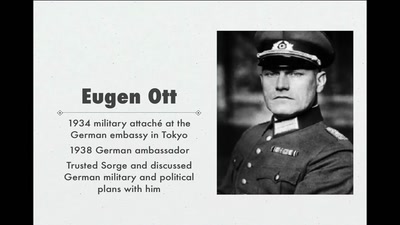
World War II Hackers
Stalin's best men, armed with paper and pen
43 min
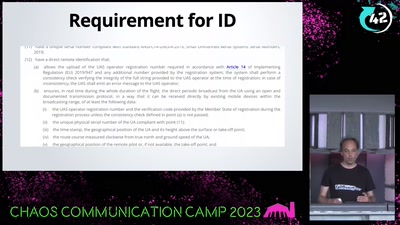
WTF DJI, UAV CTF?!
A hacker's view at commercial drone security
62 min
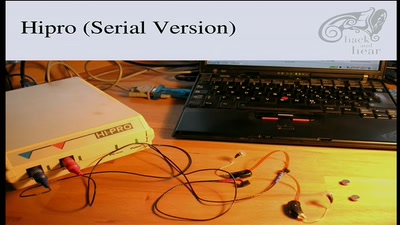
Bionic Ears
Introduction into State-of-the-Art Hearing Aid Technology
53 min
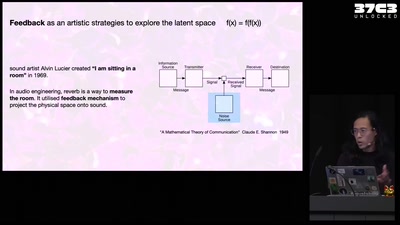
Self-cannibalizing AI
Artistic Strategies to expose generative text-to-image…
63 min
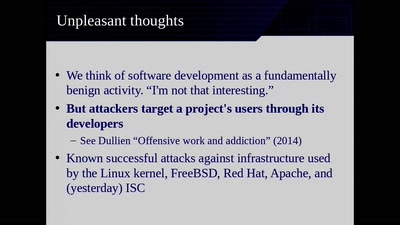
Reproducible Builds
Moving Beyond Single Points of Failure for Software…
58 min
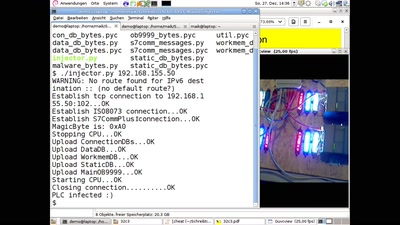
PLC-Blaster
Ein Computerwurm für PLCs
38 min
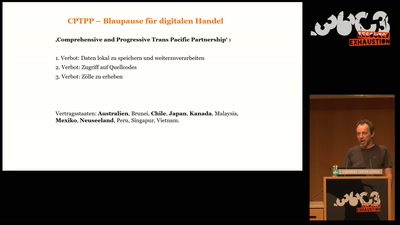
Gerechtigkeit 4.0
Makroökonomische Auswirkungen der Digitalisierung auf den…
21 min