Search for "Victor Toso" returned 180 results
30 min
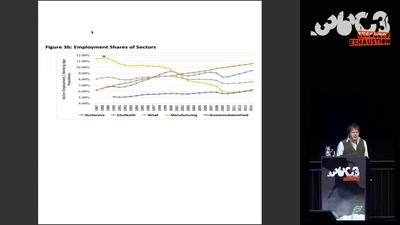
On Computing Numbers, with an Application to Problems of our Society
Journalism ♥ Computer Science
31 min
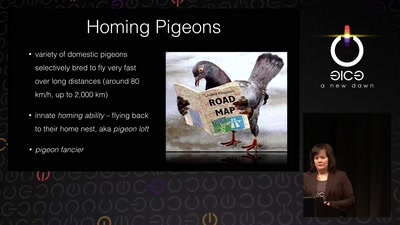
Living Drones
From war pigeons in 1914 to cyborg moths in 2014
58 min
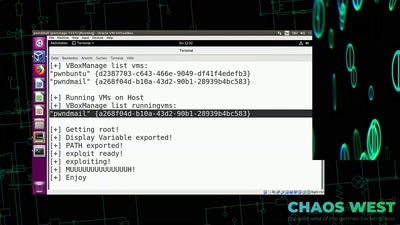
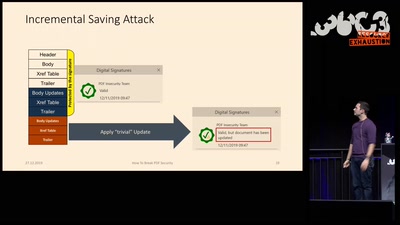
How to Break PDFs
Breaking PDF Encryption and PDF Signatures
41 min
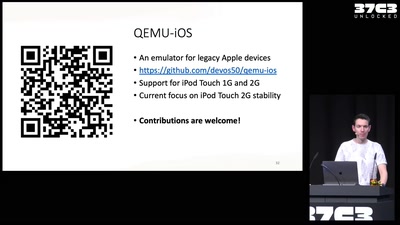
Breathing Life into Legacy: An Open-Source Emulator of Legacy Apple Devices
A Dive into Reverse Engineering and Understanding the iPod…
57 min
TrustZone-M(eh): Breaking ARMv8-M's security
Hardware attacks on the latest generation of ARM Cortex-M…
59 min
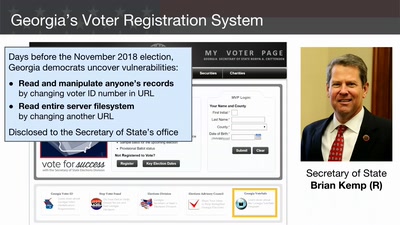
Election Cybersecurity Progress Report
Will the U.S. be ready for 2020?
56 min
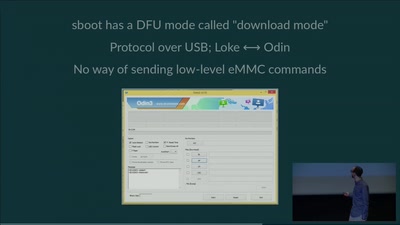
eMMC hacking, or: how I fixed long-dead Galaxy S3 phones
A journey on how to fix broken proprietary hardware by…
60 min
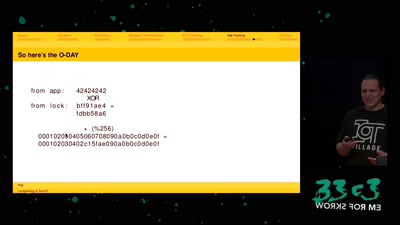
Lockpicking in the IoT
...or why adding BTLE to a device sometimes isn't smart at…

64 min
Cory Doctorow – Fireside Chat
Reading and Q&A
60 min
Concepts for global TSCM
getting out of surveillance state mode
55 min
Cat & Mouse: Evading the Censors in 2018
Preserving access to the open Internet with circumvention…
63 min
goto fail;
exploring two decades of transport layer insecurity
38 min
Unpacking the compromises of Aadhaar, and other digital identities inspired by it
Governments around the world are implementing digital…
60 min
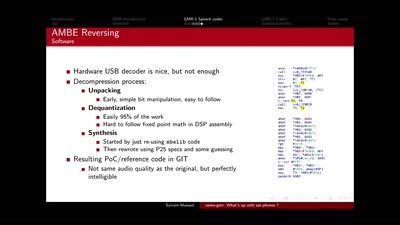
osmo-gmr: What's up with sat-phones ?
Piecing together the missing bits
61 min