Search for "Sec" returned 2734 results

41 min
Extracting keys from FPGAs, OTP Tokens and Door Locks
Side-Channel (and other) Attacks in Practice
40 min
Never Forgetti
a didactic live-gaming performance about dying women across…
59 min
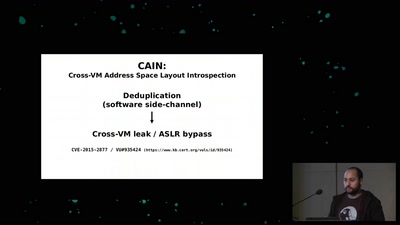
Memory Deduplication: The Curse that Keeps on Giving
A tale of 3 different memory deduplication based…
32 min
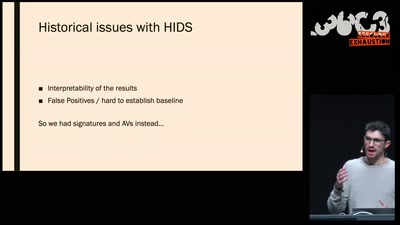
The Case for Scale in Cyber Security
Security Track Keynote
42 min
Zentrum für Politische Schönheit:
Ein Jahr Adenauer SRP+ und der Walter Lübcke Memorial Park
47 min
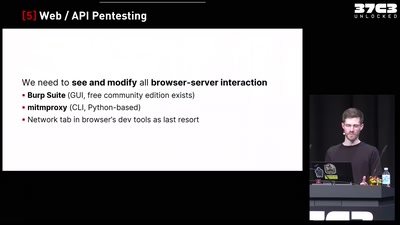
Finding Vulnerabilities in Internet-Connected Devices
A Beginner’s Guide
60 min
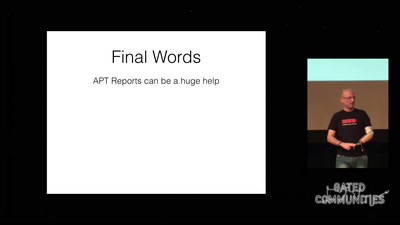
APT Reports and OPSEC Evolution, or: These are not the APT reports you are looking for
How advanced threat actors learn and change with innovation…
61 min
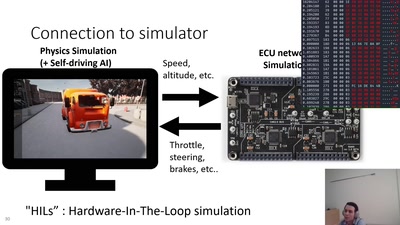
RAMN: Resistant Automotive Miniature Network
A safe platform to study and research automotive systems
59 min
Top X* usability obstacles
*(will be specified later based on usability test with…
51 min
Virtual Secure Boot
Secure Boot support in qemu, kvm and ovmf.
46 min
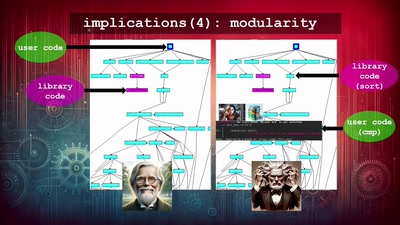
Writing secure software
using my blog as example
39 min
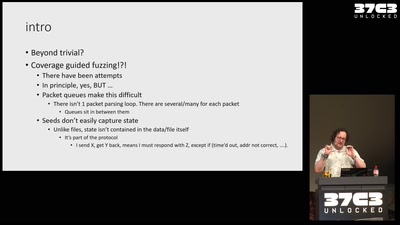
Fuzzing the TCP/IP stack
beyond the trivial
61 min