Search for "olf" returned 7516 results
60 min
Why is GPG "damn near unusable"?
An overview of usable security research
62 min
Post Memory Corruption Memory Analysis
Automating exploitation of invalid memory writes
63 min
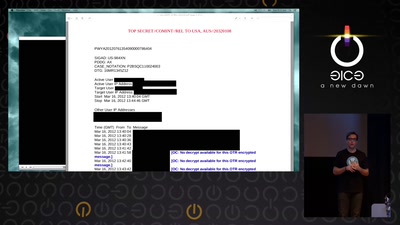
Reconstructing narratives
transparency in the service of justice
31 min
PUFs, protection, privacy, PRNGs
an overview of physically unclonable functions
66 min
borgbackup
the holy grail of backup software?
40 min
peer to peer communism vs the client-server state
The Political Economy of Network Topologies

47 min
Software Patenting
Adequate means of protection for software.
46 min
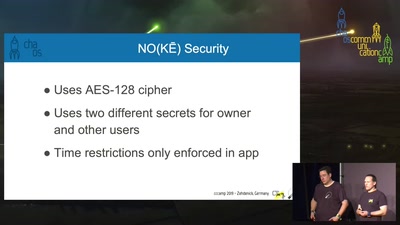
Taking Bluetooth lockpicking to the next level
...or the 37th floor of a Hotel
56 min
Protesting in the new Millenium
The Use of Electronic Communications to Protest

45 min
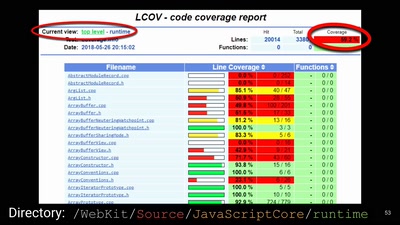
Finding and Preventing Buffer Overflows
An overview of static and dynamic approaches
29 min
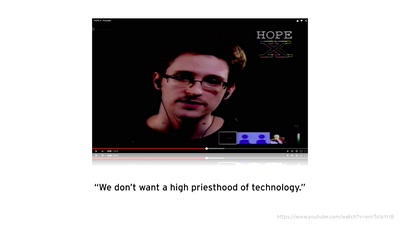
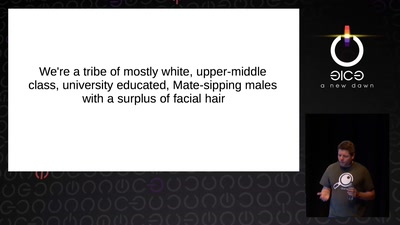
Infocalypse now: P0wning stuff is not enough
Several failure modes of the hacker scene
57 min
802.11 Packets in Packets
A Standard-Compliant Exploit of Layer 1
59 min
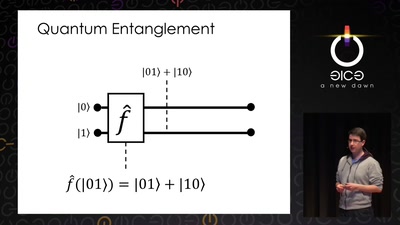
Let's build a quantum computer!
Understanding the architecture of a quantum processor

62 min
Vehicular Communication and VANETs
The future and security of communicating vehicles
57 min
The Layman's Guide to Zero-Day Engineering
A demystification of the exploit development lifecycle
57 min
600k QPS on MySQL Galera cluster
the tale of 600.000 queries per second

46 min