Search for "sven" returned 2170 results
48 min
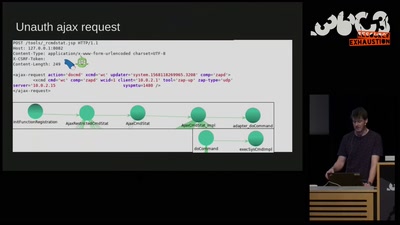
Don't Ruck Us Too Hard - Owning Ruckus AP Devices
3 different RCE vulnerabilities on Ruckus Wireless access…

33 min
Global Civil Society Under Attack
Reports from the Frontlines

32 min
Finding the Weak Crypto Needle in a Byte Haystack
Automatic detection of key-reuse vulnerabilities
57 min
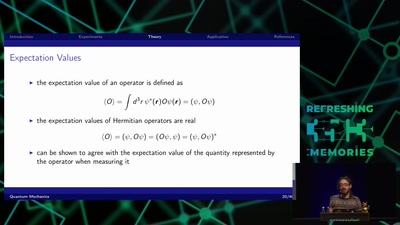
Quantum Mechanics
A Gentle Introduction

51 min
Funky File Formats
Advanced binary tricks

61 min
"The" Social Credit System
Why It's Both Better and Worse Than We can Imagine
30 min
The ArduGuitar
An Arduino Powered Electric Guitar

42 min
Citzens or subjects? The battle to control our bodies, speech and communications
A call to action to defend our ePrivacy and eliminate…

60 min
Attacking end-to-end email encryption
Efail, other attacks and lessons learned.

62 min
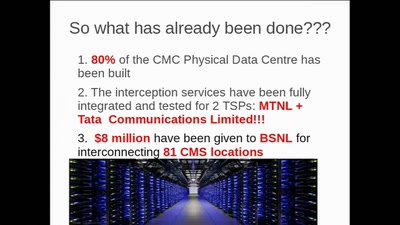
To Protect And Infect, Part 2
The militarization of the Internet
21 min
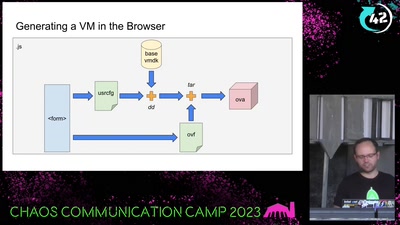
Bootloader Crimes
Building disposable Windows VMs

60 min