Search for "Sven" returned 2173 results

45 min
Tech(no)fixes beware!
Spotting (digital) tech fictions as replacement for social…

61 min
Ten years after ‚We Lost The War‘
The future does not look much brighter than ten years ago.…

62 min
To Protect And Infect, Part 2
The militarization of the Internet
65 min
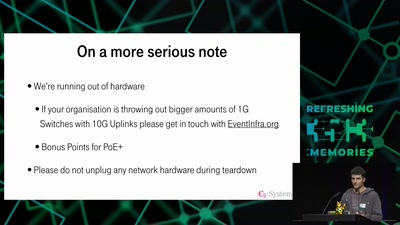
35C3 Infrastructure Review
Up and to the right: All the statistics about this event…
48 min
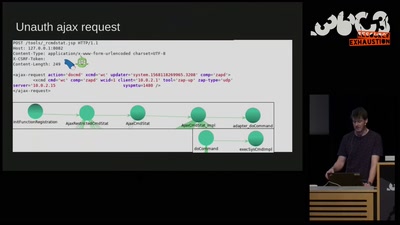
Don't Ruck Us Too Hard - Owning Ruckus AP Devices
3 different RCE vulnerabilities on Ruckus Wireless access…
30 min
On Computing Numbers, with an Application to Problems of our Society
Journalism ♥ Computer Science

60 min
Quantum Cryptography
from key distribution to position-based cryptography
32 min
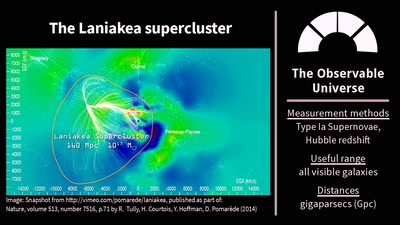
The Universe Is, Like, Seriously Huge
Stuff in Space Is Far Away – but How Do We Know?

55 min
What is Good Technology?
Answers & practical guidelines for engineers.

32 min
Finding the Weak Crypto Needle in a Byte Haystack
Automatic detection of key-reuse vulnerabilities
62 min
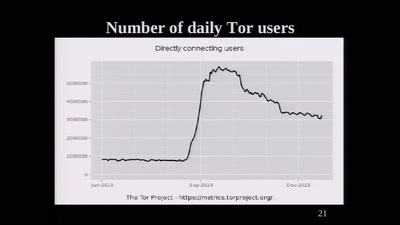
The Tor Network
We're living in interesting times

61 min