Search for "Andi" returned 7435 results

61 min
Trustworthy secure modular operating system engineering
fun(ctional) operating system and security protocol…
![for women in "${tech[@]}"; do](https://static.media.ccc.de/media/conferences/camp2015/6774-hd.jpg)
26 min
for women in "${tech[@]}"; do
Let's talk, share and learn from each other.
60 min
Resisting Surveillance: it's is not just about the metadata
The infiltration and physical surveillance of social…
58 min
Advanced memory forensics: The Cold Boot Attacks
Recovering keys and other secrets after power off

47 min
What you thought you knew about C
Impacts of undefined behaviour and other C oddities

59 min
Say hi to your new boss: How algorithms might soon control our lives.
Discrimination and ethics in the data-driven society

51 min
How to contribute to make open hardware happen
Mooltipass, Openpandora/Pyra and Novena/Senoko: how I…
21 min
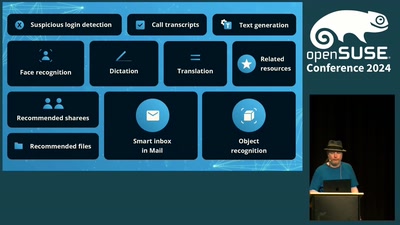
Another Approach to AI
An approach to ethical AI focussed on transparency and…

58 min
Live: Cross Collaboration Panel
How projects work together and improve open source together.
62 min
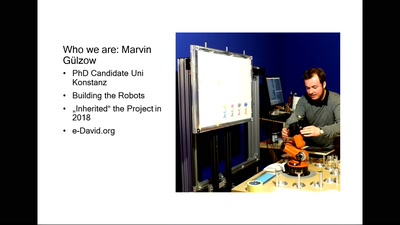
Transhuman Expression
Interdisciplinary research in Painting and Robotics. with…
56 min
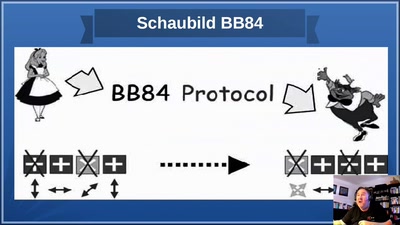
God does not play dice!
an introduction to quantum cryptography for sysadmins and…

32 min
Cryptokids
empower kids and provide tools for them to be more secure…
26 min
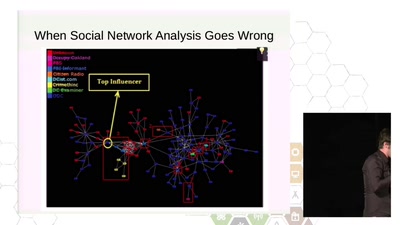
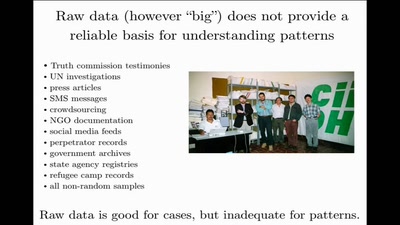
Data Mining for Good
Using random sampling, entity resolution, communications…
60 min
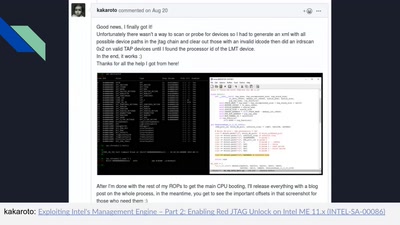
Intel Management Engine deep dive
Understanding the ME at the OS and hardware level
74 min
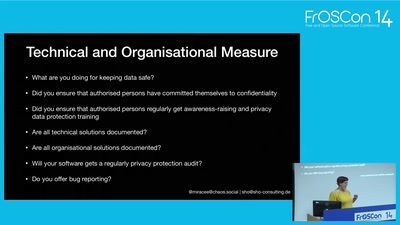
Privacy by design
how to code GDPR and e-privacy regulation safe
25 min
30 seconds to Code
Streamlining development setups with Docker and Open Build…

66 min
Podjournalism
The Role of Podcasting in Critical and Investigative…
52 min
The Youth Hostel
An odyssey in the margins of software and paper

34 min
Digital Musical Instruments
Evolution and design of new interfaces for musical…
36 min
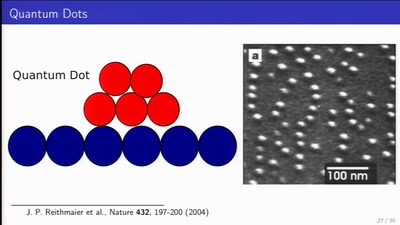
Long Distance Quantum Communication
Concepts and components for intercontinal communication…
56 min
Hacking ideologies, part 2: Open Source, a capitalist movement
Free Software, Free Drugs and an ethics of death
62 min
The Internet (Doesn't) Need Another Security Guide
Creating Internet Privacy and Security Resources That Don't…
64 min
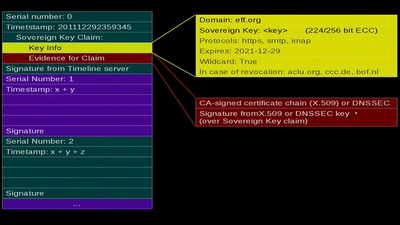
Sovereign Keys
A proposal for fixing attacks on CAs and DNSSEC
60 min
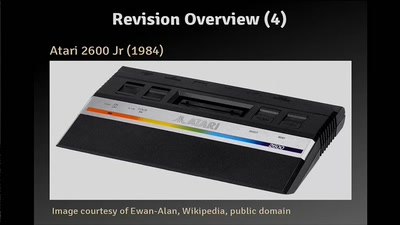
The Atari 2600 Video Computer System: The Ultimate Talk
The history, the hardware and how to write programs

60 min