Search for "BeF" returned 6082 results

32 min
Finding the Weak Crypto Needle in a Byte Haystack
Automatic detection of key-reuse vulnerabilities
30 min
SPAM, SPAM, SPAM - SPAM, SPIT und SPOM
Eine mehr oder weniger ernst gemeinte Betrachtung der…
62 min
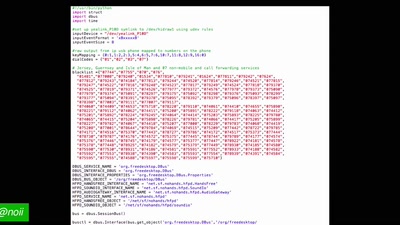
Superheroes Still Need Phoneboxes
The art of making a free phonebox and the culture of…
52 min
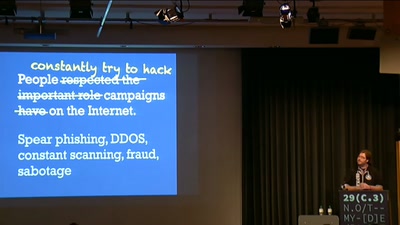
Securing the Campaign
Security and the 2012 US Presidential Election
58 min
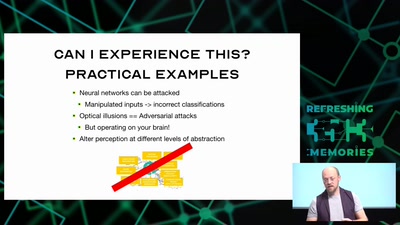
Hacking how we see
A way to fix lazy eye?
53 min