Search for "Nina" returned 474 results
62 min
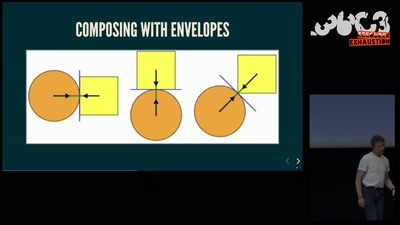
Getting software right with properties, generated tests, and proofs
Evolve your hack into robust software!
54 min
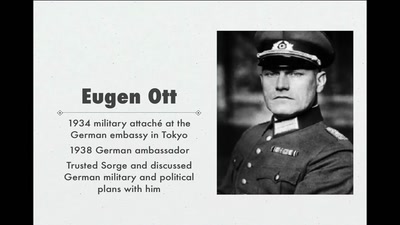
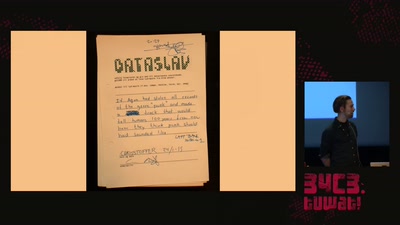
World War II Hackers
Stalin's best men, armed with paper and pen
64 min
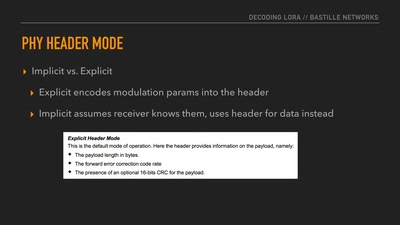
Decoding the LoRa PHY
Dissecting a Modern Wireless Network for the Internet of…
62 min
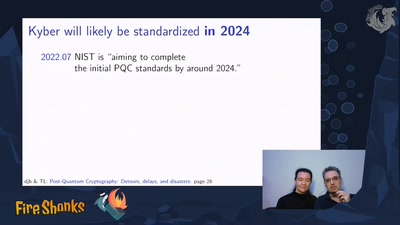
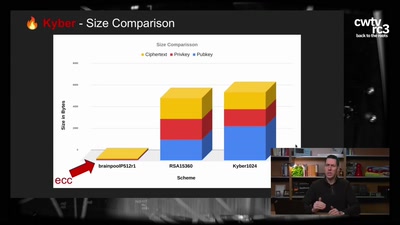
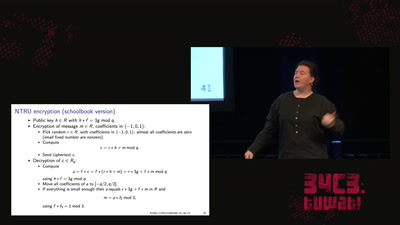
Kyber and Post-Quantum Crypto
How does it work?
50 min
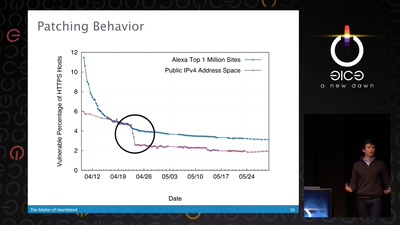
The Matter of Heartbleed
What went wrong, how the Internet reacted, what we can…
30 min
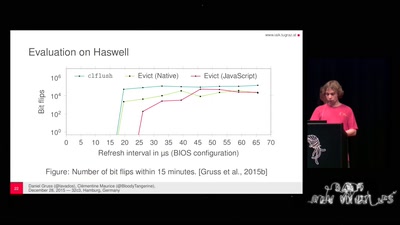
Rowhammer.js: Root privileges for web apps?
A tale of fault attacks on DRAM and attacks on CPU caches
53 min
Million Dollar Dissidents and the Rest of Us
Uncovering Nation-State Mobile Espionage in the Wild

61 min
Deploying TLS 1.3: the great, the good and the bad
Improving the encrypted the web, one round-trip at a time
60 min
G’scheitern
The art of failure taught by improv theatre

39 min
Gamified Control?
China's Social Credit Systems

31 min
Extended DNA Analysis
Political pressure for DNA-based facial composites
33 min
Robot Music
The Robots Play Our Music and What Do We Do?
64 min
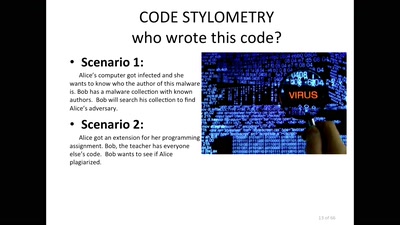
Source Code and Cross-Domain Authorship Attribution
The Role of Stylometry in Privacy
64 min
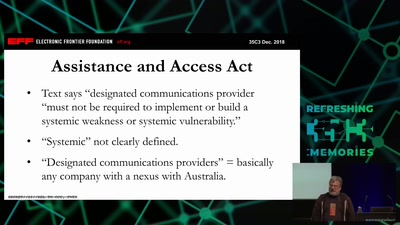
It Always Feels Like the Five Eyes Are Watching You
Five Eyes’ Quest For Security Has Given Us Widespread…
61 min
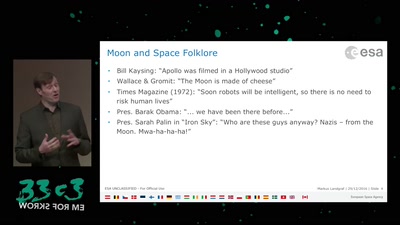
An Elevator to the Moon (and back)
Space Transportation and the Extraterrestrial Imperative
65 min