Search for "Seth Hardy" returned 901 results
63 min
Reconstructing narratives
transparency in the service of justice
58 min
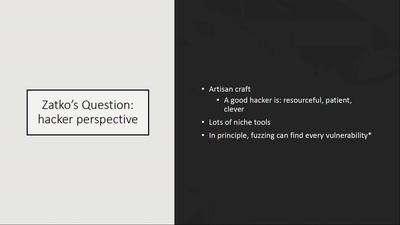
How risky is the software you use?
CITL: Quantitative, Comparable Software Risk Reporting
62 min
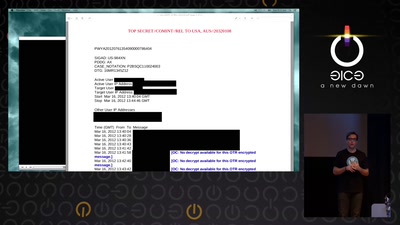
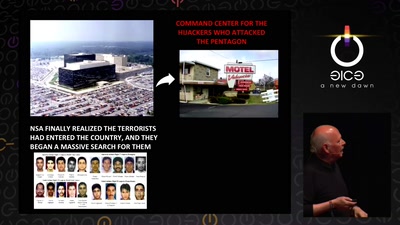
Tell no-one
A century of secret deals between the NSA and the telecom…

31 min
Demystifying Network Cards
Things you always wanted to know about NIC drivers
62 min
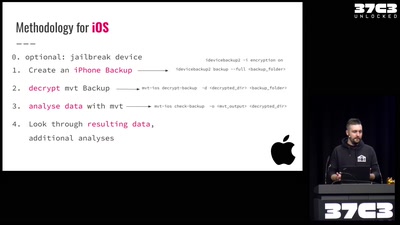
Einführung in Smartphone Malware Forensik
Wie man Stalkerware und Staatstrojaner auf Smartphones…
54 min
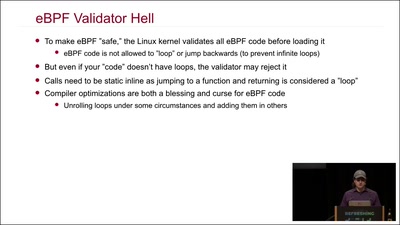
Kernel Tracing With eBPF
Unlocking God Mode on Linux
60 min
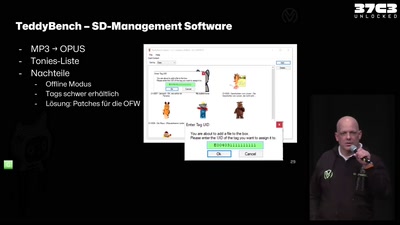
Toniebox Reverse Engineering
Eine Musikbox für Kinder, Maker und Hacker

34 min
Scuttlebutt
The decentralized P2P gossip protocol
38 min
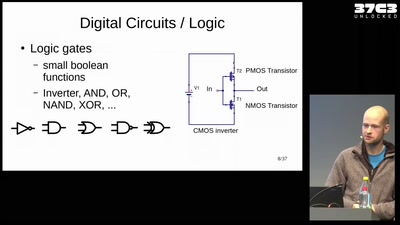
Place & route on silicon
A gentle introduction to place & route algorithms for…

45 min
HbbTV Security
OMG - my Smart TV got pr0wn3d
60 min
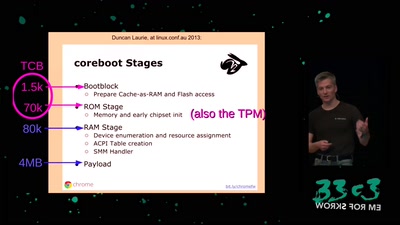
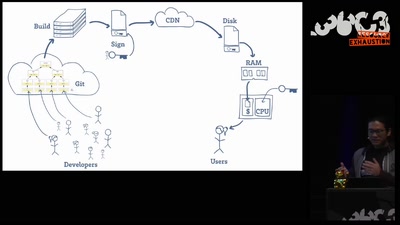
Open Source is Insufficient to Solve Trust Problems in Hardware
How Betrusted Aims to Close the Hardware TOCTOU Gap
33 min
Retail Surveillance / Retail Countersurveillance
50 most unwanted retail surveillance technologies / 50 most…
60 min
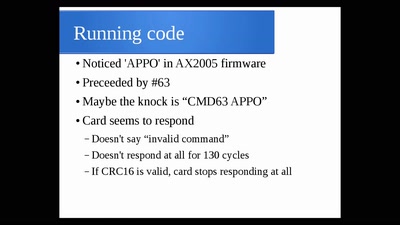
The Exploration and Exploitation of an SD Memory Card
by xobs & bunnie
60 min