Search for "ceres-c" returned 221 results
61 min
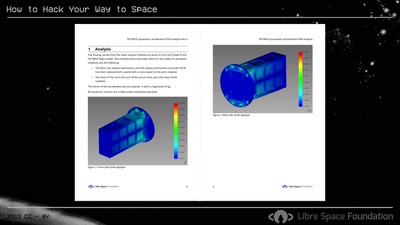
How to Hack Your Way to Space
Bringing the Hacker Mindset to the Space Ecosphere - The…
39 min
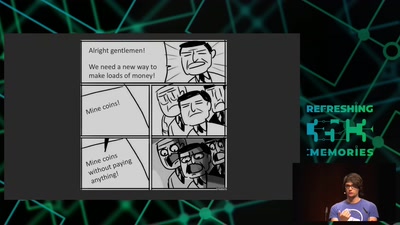
Web-based Cryptojacking in the Wild
When your browser is mining coins for other people

32 min
Verified Firewall Ruleset Verification
Math, Functional Programming, Theorem Proving, and an…

60 min
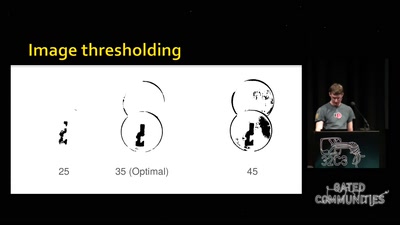
What does Big Brother see, while he is watching?
Uncovering images from the secret Stasi archives.
35 min
Ethics in the data society
Power and politics in the development of the driverless car

40 min
Radical Digital Painting
Fantastic Media Manipulation

61 min
"The" Social Credit System
Why It's Both Better and Worse Than We can Imagine

59 min
Security of the IC Backside
The future of IC analysis
66 min
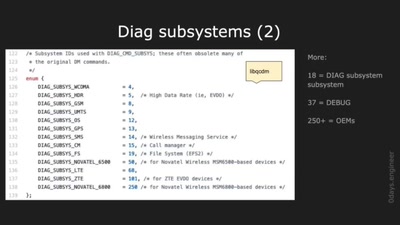
Advanced Hexagon Diag
Harnessing diagnostics for baseband vulnerability research
60 min
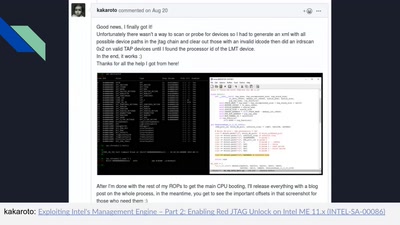
Intel Management Engine deep dive
Understanding the ME at the OS and hardware level
59 min
Top X* usability obstacles
*(will be specified later based on usability test with…
43 min
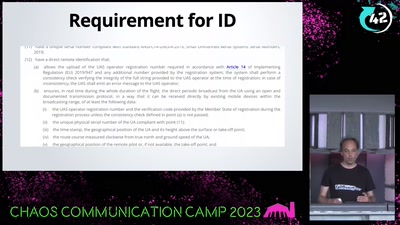
WTF DJI, UAV CTF?!
A hacker's view at commercial drone security
60 min
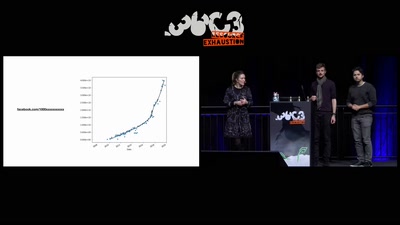
Inside the Fake Like Factories
How thousands of Facebook, You Tube and Instagram pages…
58 min
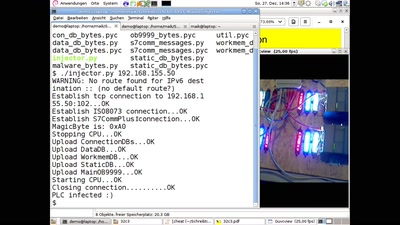
PLC-Blaster
Ein Computerwurm für PLCs
61 min
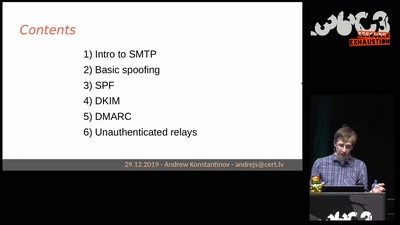
Email authentication for penetration testers
When SPF is not enough

62 min
Corporate surveillance, digital tracking, big data & privacy
How thousands of companies are profiling, categorizing,…
44 min
Replication Prohibited
3D printed key attacks
58 min