Search for "jk" returned 2324 results
55 min
ZombieLoad Attack
Leaking Your Recent Memory Operations on Intel CPUs

60 min
Quantum Cryptography
from key distribution to position-based cryptography
61 min
Damn Vulnerable Chemical Process
Exploitation in a new media
60 min
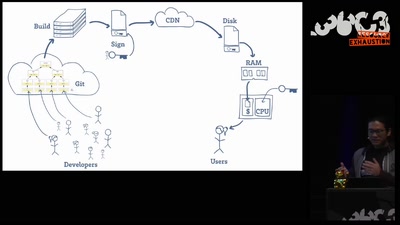
Open Source is Insufficient to Solve Trust Problems in Hardware
How Betrusted Aims to Close the Hardware TOCTOU Gap
51 min
Virtual Secure Boot
Secure Boot support in qemu, kvm and ovmf.

59 min
Hacking EU funding for a decentralizing FOSS project
Understanding and adapting EU legal guidelines from a FOSS…
57 min
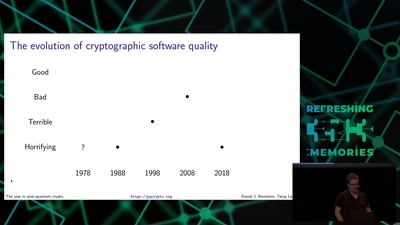
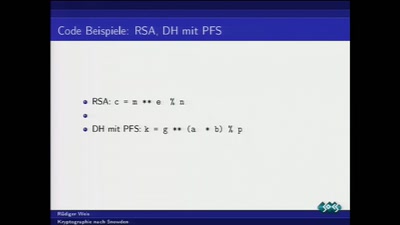
Kryptographie nach Snowden
Was tun nach der mittelmäßigen Kryptographie-Apokalypse?
49 min
Electromagnetic Threats for Information Security
Ways to Chaos in Digital and Analogue Electronics
60 min
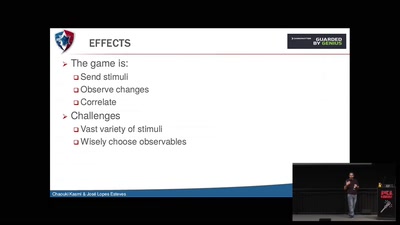
APT Reports and OPSEC Evolution, or: These are not the APT reports you are looking for
How advanced threat actors learn and change with innovation…
62 min
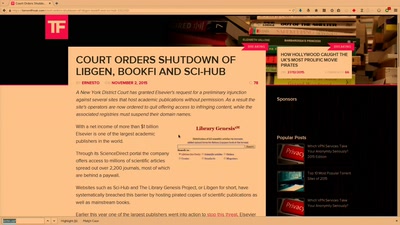
Public Library/Memory of the World
Access to knowledge for every member of society
42 min
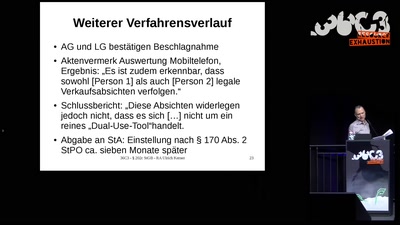
Hackerparagraph § 202c StGB // Reality Check
Cybercrime-Ermittlungen: Vorsicht vor der Polizei! Oder:…
61 min