Search for "Gui" returned 1833 results
60 min
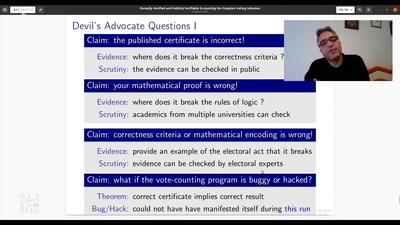
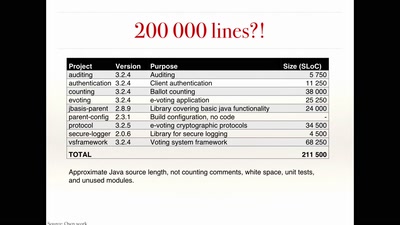
The rise and fall of Internet voting in Norway
Evaluating a complex cryptographic implementation
64 min
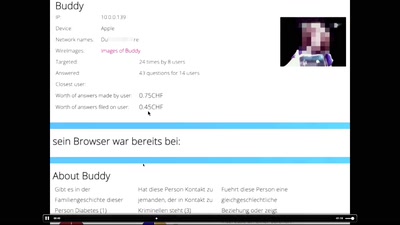
"Exploit" in theater
post-existentialism is the question, not post-privacy
55 min
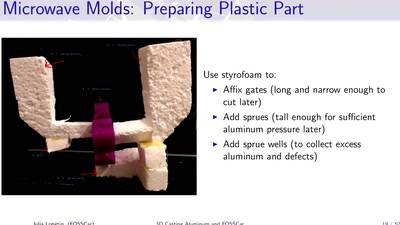
3D Casting Aluminum
Too Much Fun with Microwaves
58 min
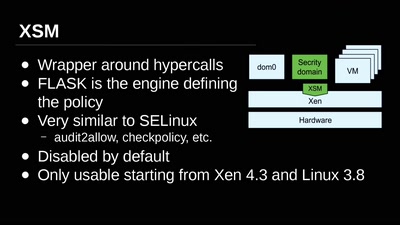
Virtual Machine Introspection
From the Outside Looking In
60 min
Check your privileges!
How to drop more of your privileges to reduce attack…
30 min
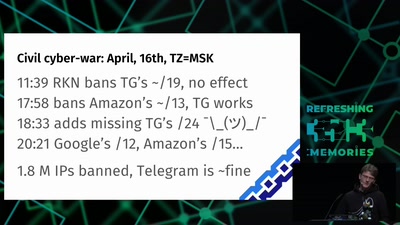
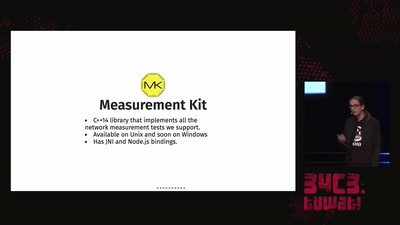
OONI: Let's Fight Internet Censorship, Together!
The Open Observatory of Network Interference

59 min
Security of the IC Backside
The future of IC analysis

55 min
What is Good Technology?
Answers & practical guidelines for engineers.
62 min
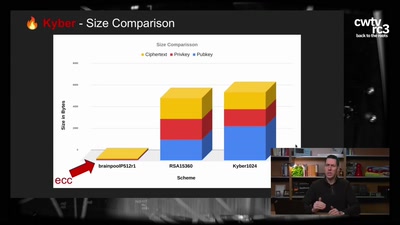
Kyber and Post-Quantum Crypto
How does it work?
91 min
What the World can learn from Hongkong
From Unanimity to Anonymity
63 min
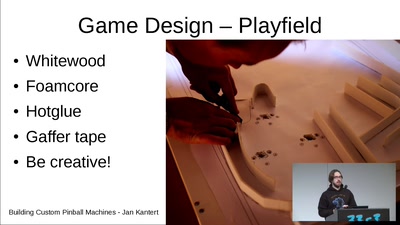
Building Custom Pinball Machines
What you need and how it works. An experiences report

61 min
Correcting copywrongs
European copyright reform is finally on the horizon
46 min
You can -j REJECT but you can not hide: Global scanning of the IPv6 Internet
Finding interesting targets in 128bit of entropy

61 min
Deploying TLS 1.3: the great, the good and the bad
Improving the encrypted the web, one round-trip at a time
44 min
Exploiting PHP7 unserialize
teaching a new dog old tricks
69 min
cryptocurrencies, smart contracts, etc.: revolutionary tech?
short answer: Yes!
62 min
Machine Dreams
Dreaming Machines
61 min