Search for "JO" returned 10375 results
38 min
Squeezing Attack Traces
How to get useable information out of your honeypot
58 min
Collapsing the European security architecture
More security-critical behaviour in Europe!
63 min
Exploiting Symbian
Symbian Exploit and Shellcode Development

48 min
SWF and the Malware Tragedy
Hide and Seek in A. Flash
45 min
Privacy in the social semantic web
Social networks based on XMPP
51 min
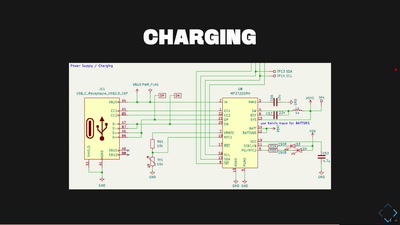
Algorithmic Music in a Box
Doing music with microcontrollers

52 min
Datenpannen
Forderungen nach dem Jahr der Datenverbrechen
55 min
Das Grundrecht auf digitale Intimsphäre
Festplattenbeschlagnahme in neuem Licht
60 min
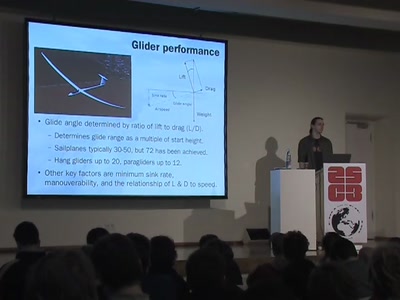
Flying for free
Exploiting the weather with unpowered aircraft
60 min
Der elektronische Personalausweis
Endlich wird jeder zum "Trusted Citizen"
51 min
Lightning Talks Day2
4 minutes of fame

70 min
Neusprech im Überwachungsstaat
Politikersprache zwischen Orwell und Online
94 min
Security Nightmares 2009
Oder: worüber wir nächstes Jahr lachen werden
65 min
eVoting after Nedap and Digital Pen
Why cryptography might not fix the issue of transparent…
82 min
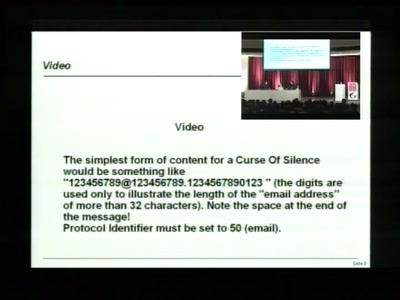
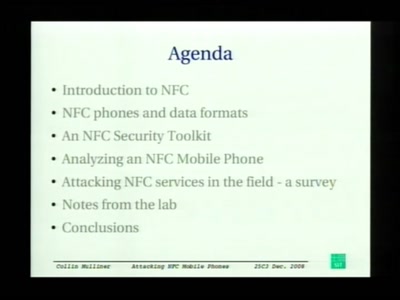
Attacking NFC mobile phones
First look at the security of NFC mobile phones
67 min
Life is a Holodeck!
An overview of holographic techniques

56 min
Console Hacking 2008: Wii Fail
Is implementation the enemy of design?
34 min
FeTAp 611 unplugged
Taking a rotary dial phone to the mobile age
29 min
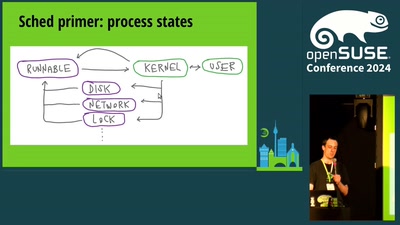
Pluggable CPU schedulers in openSUSE
How to write your own CPU scheduler with openSUSE

57 min
Android Security
bringing x86 fuckups to dalvik
37 min
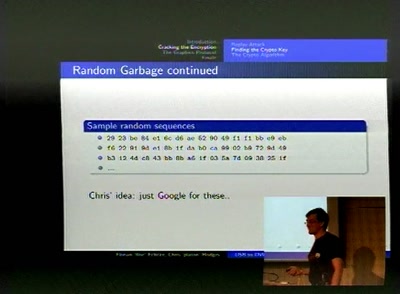
Reverse-Engineering DisplayLink devices
USB to DVI for Hackers
56 min