Search for "andz" returned 7461 results
53 min
Privaterra - Report from the field
IT Security and Human Rights organizations - The needs, the…
50 min
Data Analysis in Terabit Ethernet Traffic
Solutions for monitoring and lawful interception within a…
60 min
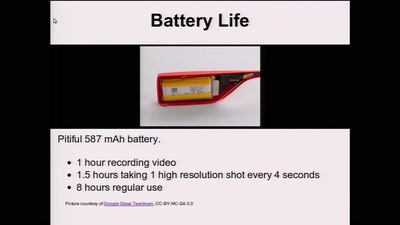
Glass Hacks
Fun and frightening uses of always-on camera enabled…
26 min
Technomonopolies
How technology is used to subvert and circumvent…
68 min
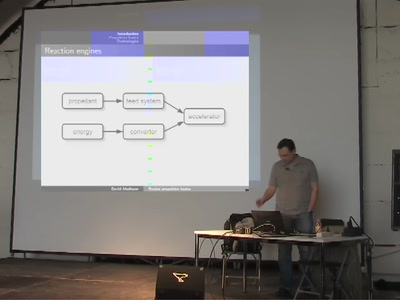
Rocket propulsion basics
An introduction to rocket engines and their application for…
24 min
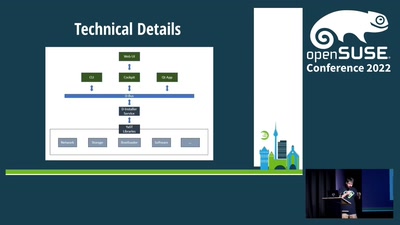
D-Installer Project: Carving a Modern Installer
A new installer based on D-Bus, YaST, Cockpit and web…
30 min
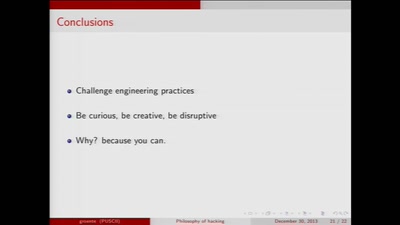
The philosophy of hacking
Contemplations on the essence of hacking and its…

71 min
Security in the cardholder data processing?!
Experiences and lessons learned with the Payment Card…
39 min
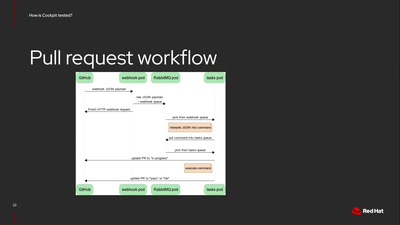
Testing software on multiple Linux distributions
How Cockpit is tested on multiple distributions and…
61 min
Human body as an electric IO system
Hacking your brain, and other body parts. Debunking myths…
33 min
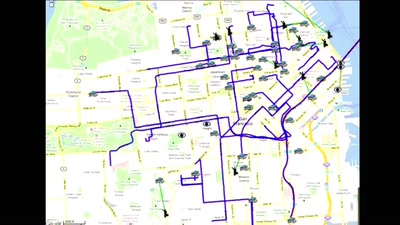
Space making/space shaping
How mapping creates space, shapes cities and our view of…

32 min
Freedom from the web's monopolies
A better architecture for the web, beneficial to both…
30 min
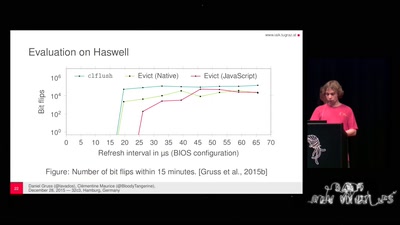
Rowhammer.js: Root privileges for web apps?
A tale of fault attacks on DRAM and attacks on CPU caches

32 min
(Virtual Talk) GitOps meets dotfiles: Never Setup a New Machine Again!
Running your Window Manager and Applications in non-root…
51 min
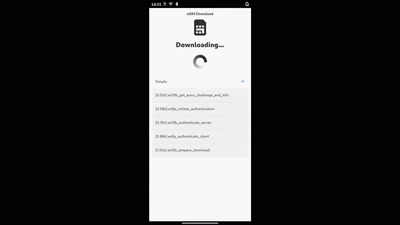
eSIM management on Qualcomm phones
Using an open-source and mainline Linux stack to work with…
57 min
The Small Device C Compiler for 8-bit firmware development
The current state and near-future plans for a central part…

43 min
The ecosystem is moving
Challenges for distributed and decentralized technology…

58 min
Es gibt keinen Löffel? Dann druck doch einen neuen aus!
How the internet, open source and fabbing are making…

56 min
Search Engines - Oracles of the Information Society
The Saga continues: Search Engines, Technology, Politics,…
29 min
Basics of hydroponics
A need to know on soilless growing before building,…
62 min
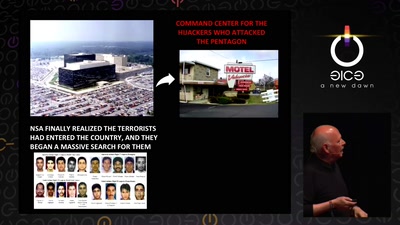
Tell no-one
A century of secret deals between the NSA and the telecom…
53 min
Fuzzing in the corporate world
The use of fuzzing in the corporate world over the years…

46 min
Etherify - bringing the ether back to ethernet
Primitive soft tempest demos: exfiltrating data via leakage…
55 min
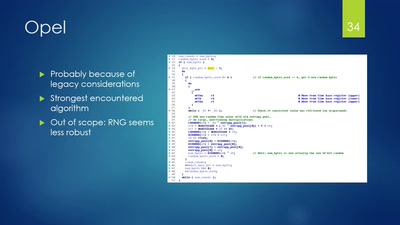
Vehicle immobilization revisited
Uncovering and assessing a second authentication mechanism…
51 min