Search for "olf" returned 7527 results
57 min
Software Reliability in Aerospace
An overview on design and generation of safe and reliable…
60 min
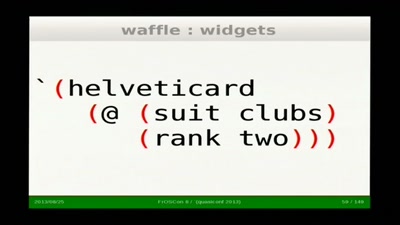
Building knodium.com with Scheme
First-hand experience report of a business application…
33 min
Computer Science in the DPRK
A view into technology on the other side of the world
43 min
#NoPNR – Let’s kill the next Data Retention Law
How to Stop the Dubious Use of Passenger Name Records by…
55 min
The good, the strange and the ugly in 2018 art &tech
On art, AI, hormones hacking and other prospects of a…

87 min
OPENCOIL – A Roaming Speedshow
or the fine art of appropriating inductive charging pads in…
52 min
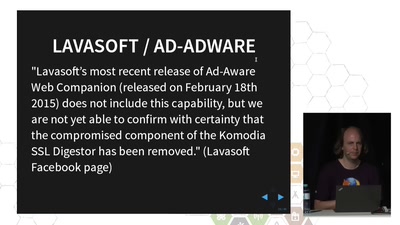
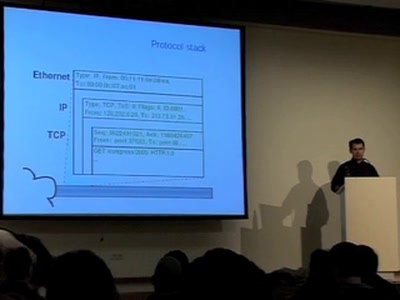
TLS interception considered harmful
How Man-in-the-Middle filtering solutions harm the security…
60 min
Lifting the Fog on Red Star OS
A deep dive into the surveillance features of North Korea's…

35 min
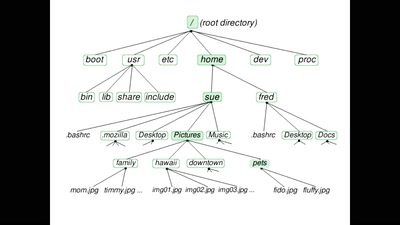
Don't Fear the Reboot
Embracing an Immutable-Friendly Mindset

60 min
The Trust Situation
Why the idea of data protection slowly turns out to be…

48 min
(Web) Search on Linux driven sites
High speed search with SPHINX or MNOGO for huge amounts of…

43 min
The ecosystem is moving
Challenges for distributed and decentralized technology…
45 min
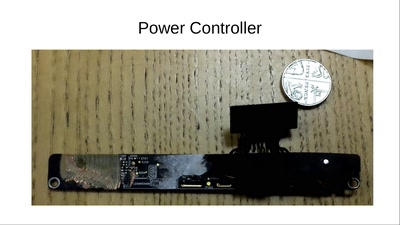
A mobile phone that respects your freedom
Experiences and lessons learned from 2 years of development…
27 min
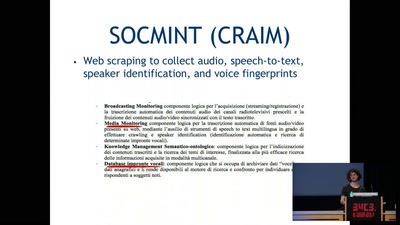
Italy's surveillance toolbox
Research on Monitoring Italian Government Surveillance…
42 min
Covert channels in TCP/IP: attack and defence
Creation and detection of IP steganography for covert…
55 min
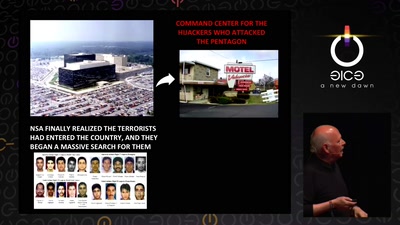
Graphs, Drones & Phones
The role of social-graphs for Drones in the War on Terror.
58 min
How to Destroy a Laptop with Top Secrets
How did GCHQ do it to the Guardian's copy of Snowden's…

138 min
We don't trust voting computers
The story of the dutch campaign against black-box voting to…
62 min