Search for "Ana" returned 10002 results

20 min
osc2 - The modern osc
Development status and how to contribute

55 min
Black Ops 2006 Viz Edition
Pixel Fuzzing and the Bioinformatic Bindiff

107 min
Hacker Jeopardy
The one and only hacker quizshow
39 min
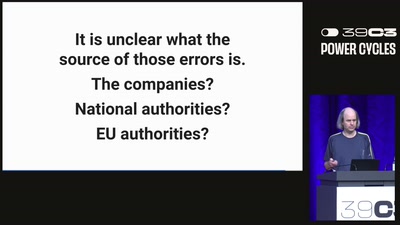
Greenhouse Gas Emission Data
Public, difficult to access, and not always correct

66 min
The Snowden Refugees under Surveillance in Hong Kong
A Rapidly Emerging Police State and Imminent Deportation to…
61 min
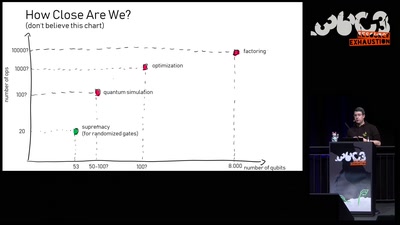
Quantum Computing: Are we there yet?
An introduction to quantum computing and a review of the…

31 min
Buffered Daemons
Sound art performance exploring the concept of translation…

37 min
Beyond Olm
About challenges and opportunities in Messaging Layer…
57 min
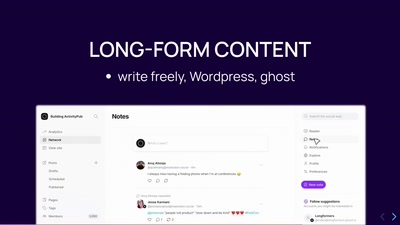
Taking a Fresh Look at the Fediverse
What Is New For Mastodon And The Wider Ecosystem

60 min
Are machines feminine?
exploring the relations between design and perception of…
21 min
DevOps for GNOME with Flatpak
And how we improved our contributors experience and…

40 min
Domain computers have accounts, too!
Owning machines through relaying and delegation
44 min
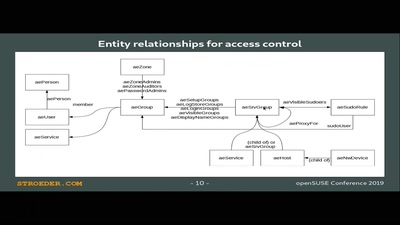
Æ-DIR -- Authorized Entitites Directory
Identity and Access Management with OpenLDAP
64 min
Fermentation Mobile
experimental, educational and commercial fermentation…
15 min
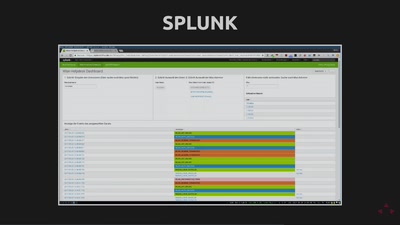
Build yourself a SNMP replacement
And make SSH pay for it

46 min
Maker Spaces in Favelas - Lecture
Engaging social innovation and social innovators
51 min
From zero to Openstack
Deploying Openstack for fun and profit
55 min
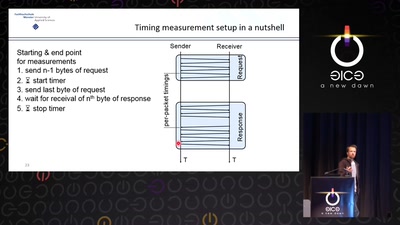
Revisiting SSL/TLS Implementations
New Bleichenbacher Side Channels and Attacks

60 min
Attacking end-to-end email encryption
Efail, other attacks and lessons learned.
42 min
We do Privacy by Design
Best practices and real-life examples

60 min
Hacking Reality
Mixed Reality and multi-sensory communication
60 min
Faster PwninG Assured
Hardware Hacks and Cracks with FPGAs
40 min
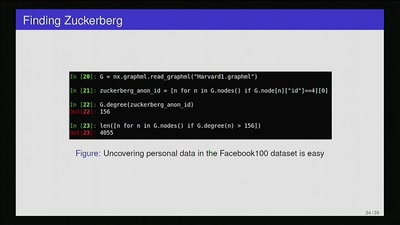
Privacy Invasion or Innovative Science?
Academia, social media data, and privacy
74 min