Search for "Sven" returned 2174 results
49 min
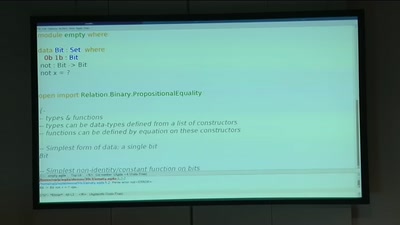
BREACH in Agda
Security notions, proofs and attacks using dependently…
58 min
CHINTERNET ART
Creativity, Archives & Digital Media from the Chinese…
51 min
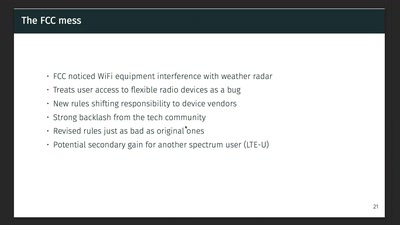
Wireless Drivers: Freedom considered harmful?
An OpenWrt perspective on the development of Linux 802.11…
48 min
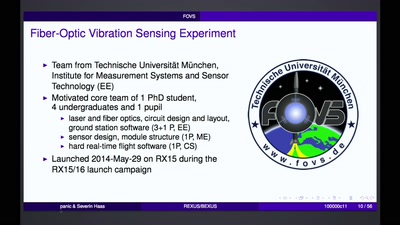
REXUS/BEXUS - Rocket and Balloon Experiments for University Students
How to bring student experiments into space.

45 min
Triggering Deep Vulnerabilities Using Symbolic Execution
Deep program analysis without the headache
64 min
"Exploit" in theater
post-existentialism is the question, not post-privacy

63 min
The Global Assassination Grid
The Infrastructure and People behind Drone Killings
51 min
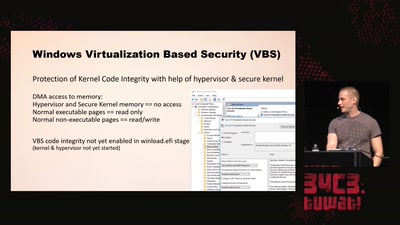
Virtual Secure Boot
Secure Boot support in qemu, kvm and ovmf.
31 min
JODI - Apache is functioning normally
A net.art collective since 1995. Understanding the browser…
55 min
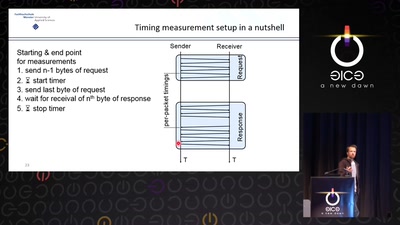
Revisiting SSL/TLS Implementations
New Bleichenbacher Side Channels and Attacks
57 min
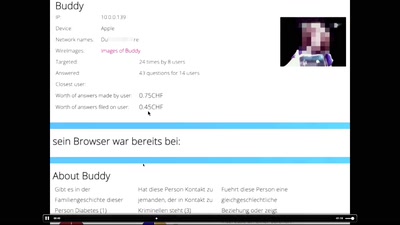
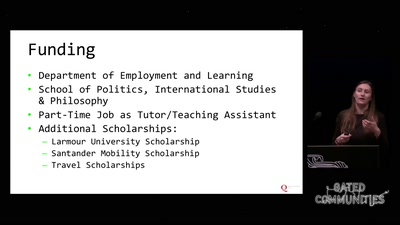
“I feel like a criminal and I have to be god at the same time”
Perceptions of hackers and hacktivists on their…
60 min