Search for "feh" returned 1866 results
53 min
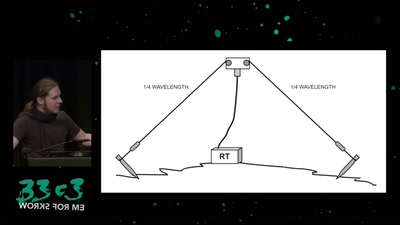
Surveilling the surveillers
About military RF communication surveillance and other…

117 min
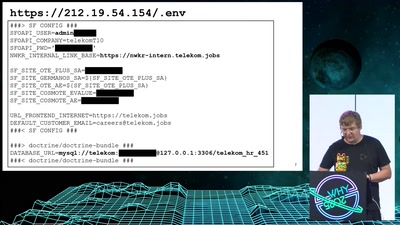
Honeypot Forensics
No stone unturned or: logs, what logs?
59 min
How to teach programming to your loved ones
Enabling students over example-driven teaching

45 min
Triggering Deep Vulnerabilities Using Symbolic Execution
Deep program analysis without the headache
59 min
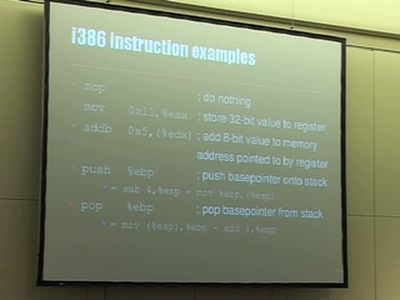
Understanding buffer overflow exploitation
The fascinating interplay of CPU, stack, C-compiler and…

32 min