Search for "Dan" returned 11698 results
60 min
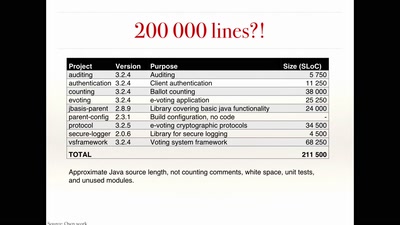
The rise and fall of Internet voting in Norway
Evaluating a complex cryptographic implementation

32 min
Finding the Weak Crypto Needle in a Byte Haystack
Automatic detection of key-reuse vulnerabilities
29 min
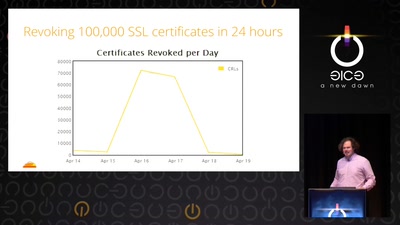
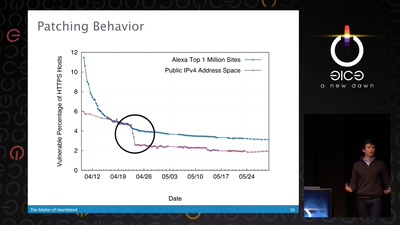
Heartache and Heartbleed: The insider’s perspective on the aftermath of Heartbleed
The untold story of what really happened, how it was…
50 min
The Matter of Heartbleed
What went wrong, how the Internet reacted, what we can…
30 min
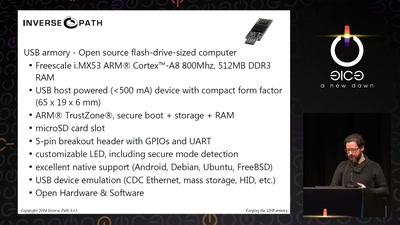
Forging the USB armory
Creating an open source secure flash-drive-sized computer

61 min
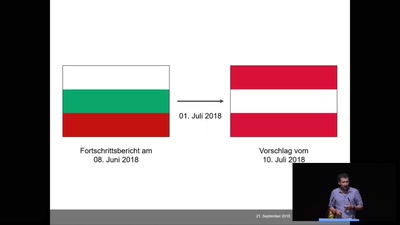
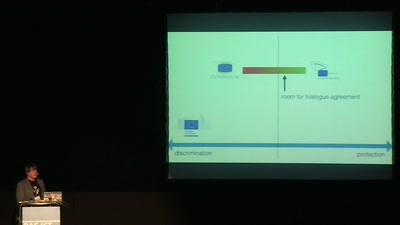
Correcting copywrongs
European copyright reform is finally on the horizon
64 min
"Exploit" in theater
post-existentialism is the question, not post-privacy

61 min
Trustworthy secure modular operating system engineering
fun(ctional) operating system and security protocol…
59 min