Search for "andi" returned 7451 results
security in 2006: having phun with it.jpg)
111 min
X.25 (in)security in 2006: having phun with it
Actual present, next future & field experiences analysis of…
63 min
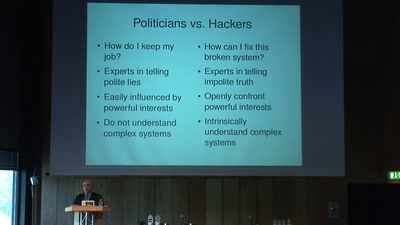
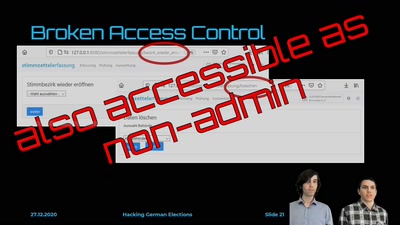
Hacking German Elections
Insecure Electronic Vote Counting - How It Returned and Why…

60 min
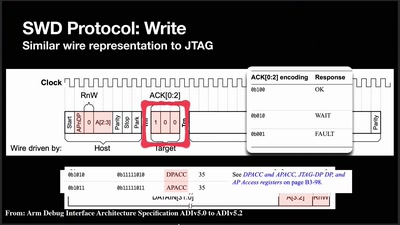
HAL - The Open-Source Hardware Analyzer
A dive into the foundations of hardware reverse engineering…
43 min
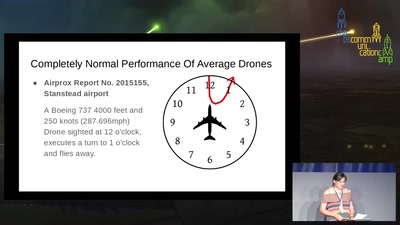
The Great British Drone Panic
Asking for better standards of official investigation and…
43 min
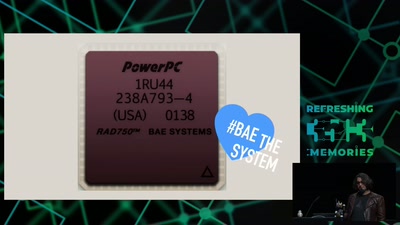
The Mars Rover On-board Computer
How Curiosity's Onboard Computer works, and what you can…
74 min
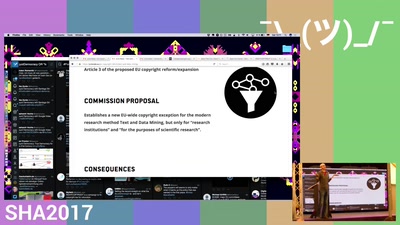
Let's stop EU copyright expansion
If you like untaxed links and unsurveilled uploads, you…

56 min
IMMI, from concept to reality
The Icelandic Modern Media Initiative and our need for a…

78 min
Stealth malware - can good guys win?
Challenges in detecting system compromises and why we’re so…
57 min
How To Design A Decent User Interface
Take a look at software from a user's point of view and…
29 min
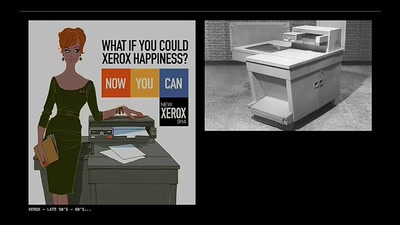
The Pirate Cinema
Creating mash-up movies by hidden activity and geography of…
49 min
A short political history of acoustics
For whom, and to do what, the science of sound was…

41 min
Chaos Communication Chemistry
DNA security systems based on molecular randomness
33 min
The GNU Health : Free Software technology improving Public Healthcare around the world
GNU Health uses Free/Libre, state-of-the-art technology to…
60 min
Build your own NSA
How private companies leak your personal data into the…

117 min
Fnord News Show
Der schonungslose Realitätsabgleich mit…
40 min
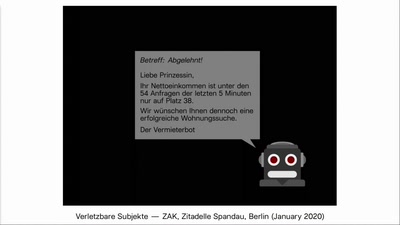
Wohnungsbot: An Automation-Drama in Three Acts
A media-art project which automates the search for flats in…
33 min
![Why we are addicted to lithium [2/2]](https://static.media.ccc.de/media/events/rc3/2021/194-17816a45-eea7-5b85-b623-5f343aec59de.jpg)


![Why we are addicted to lithium [1/2]](https://static.media.ccc.de/media/events/rc3/2021/193-3fd1b8af-9ab6-54c5-88ad-2622c1cc925a.jpg)