Search for "Ann" returned 11355 results

52 min
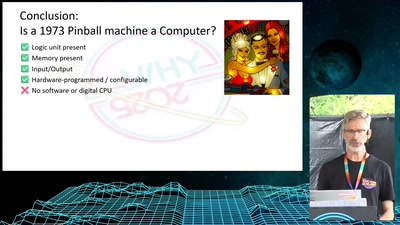
Objects as Software: The Coming Revolution
How RepRap and physical compilers will change the world as…
39 min
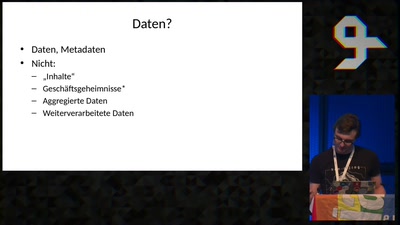
The Data must flow
Ansprüche auf Datenzugang und wer da so drauf zugreifen kann
65 min
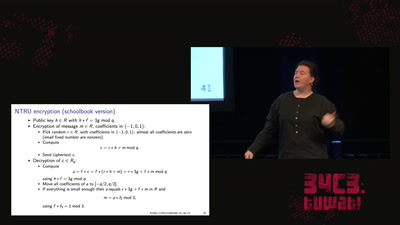
LatticeHacks
Fun with lattices in cryptography and cryptanalysis
28 min
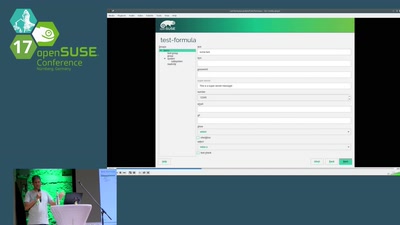
Adding Salt to AutoYaST
Integration between AutoYaST and Configuration Management…
32 min
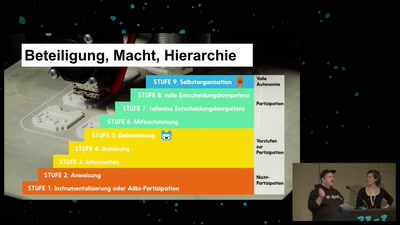
Von Alpakas, Hasenbären und Einhörnern – Über Anerkennungskultur
Wie Wertschätzung in (Tech-)Communities gelingen kann
43 min
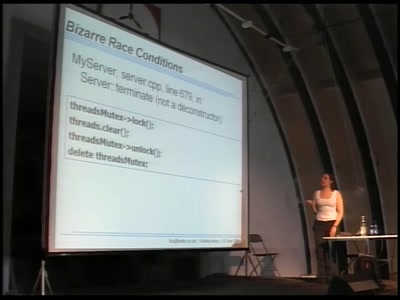
Twisting timing in your favour
Finding and exploiting concurrency issues in software
55 min
"How I met your pointer"
Hijacking client software for fuzz and profit
54 min
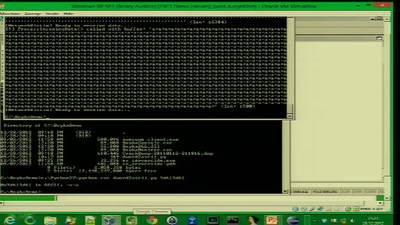
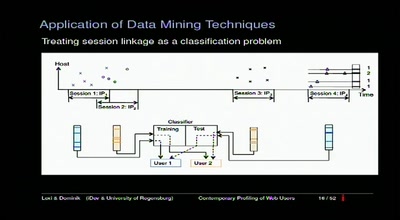
Contemporary Profiling of Web Users
On Using Anonymizers and Still Get Fucked
55 min
Steal Everything, Kill Everyone, Cause Total Financial Ruin!
Or: How I walked in and misbehaved
47 min
Ein Jahr Serverless
The good, the bad and the ugly
36 min
PolyCoin - A game played across MCH
How it works and what is inside it
61 min
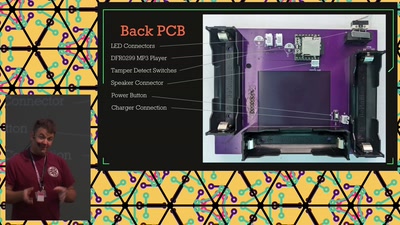
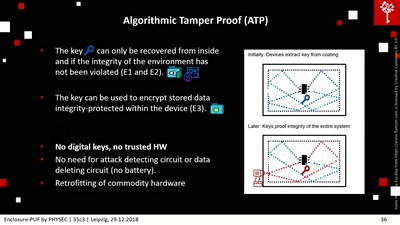
Enclosure-PUF
Tamper Proofing Commodity Hardware and other Applications
36 min
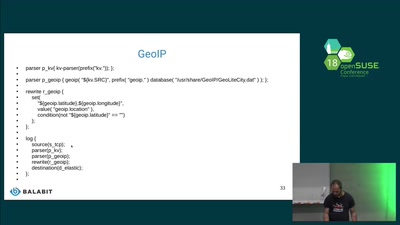
Logging containers
Collecting host, docker and container logs centrally

73 min
DG74: Bitcoin
Privacy and Censorship Resistance Beyond the Web
58 min
Physical Security
The Good, the Bad and the Ugly

49 min
Digital Signal Processors
What? Why? And how to get started
31 min
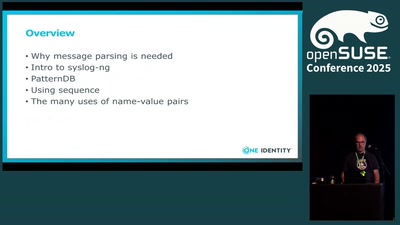
Fine tuning log routing
How sequence and creating name-value pairs can help you
54 min
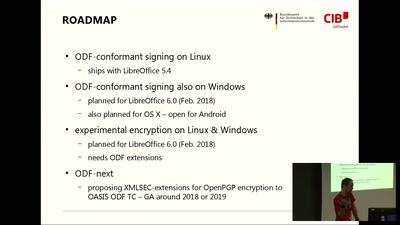
gpg4libre - OpenPGP signing & encryption in LibreOffice
Transparently and securely use your existing keys to sign…
46 min
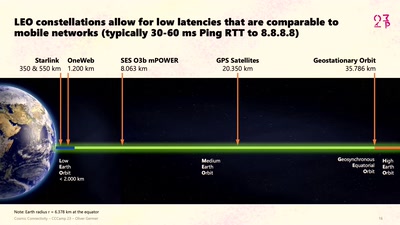
Cosmic Connectivity
Starlink, Satellite Swarms, and the Hackers' Final Frontier

29 min
Edible Soft Robotics
An exploration of candy as an engineered material
55 min
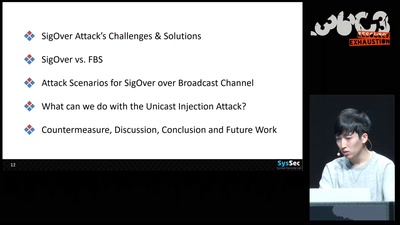
SigOver + alpha
Signal overshadowing attack on LTE and its applications
42 min