Search for "Mo" returned 10605 results
62 min
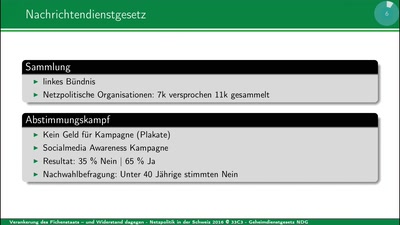
Netzpolitik in der Schweiz 2016
Grundrechte per Volksentscheid versenken
60 min
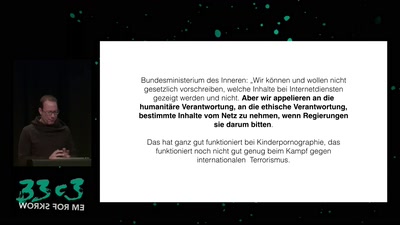
Privatisierung der Rechtsdurchsetzung
Was der Anti-Terror-Kampf von der Urheberrechtsdurchsetzung…

58 min
Security Failures in Smart Card Payment Systems
Tampering the Tamper-Proof
34 min
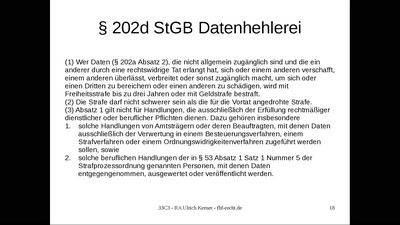
Haft für Whistleblower?
Demokratiefeindliches Strafrecht: Die Datenhehlerei gem. §…
61 min
Attacking Rich Internet Applications
Not your mother's XSS bugs

29 min
Edible Soft Robotics
An exploration of candy as an engineered material
63 min
Banking Malware 101
Overview of Current Keylogger Threats
66 min
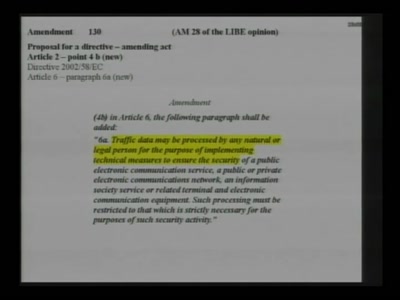
La Quadrature du Net - Campaigning on Telecoms Package
Pan-european activism for patching a "pirated" law

49 min
Beyond Asimov - Laws for Robots
Developing rules for autonomous systems

52 min
Objects as Software: The Coming Revolution
How RepRap and physical compilers will change the world as…
27 min
Romantic Hackers
Keats, Wordsworth and Total Surveillance
61 min
Hackers As A High-Risk Population
Harm Reduction Methodology

61 min
Copywrongs 2.0
We must prevent EU copyright reform from breaking the…
138 min