Search for "Mo" returned 10605 results

49 min
Beyond Asimov - Laws for Robots
Developing rules for autonomous systems

52 min
Objects as Software: The Coming Revolution
How RepRap and physical compilers will change the world as…
27 min
Romantic Hackers
Keats, Wordsworth and Total Surveillance
61 min
Hackers As A High-Risk Population
Harm Reduction Methodology
138 min
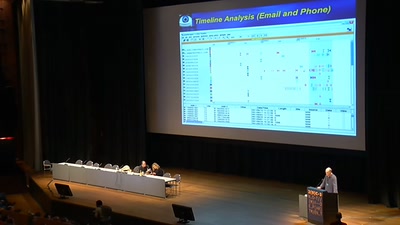
Enemies of the State: What Happens When Telling the Truth about Secret US Government…
Blowing the Whistle on Spying, Lying & Illegalities in the…
58 min
Advanced memory forensics: The Cold Boot Attacks
Recovering keys and other secrets after power off
66 min
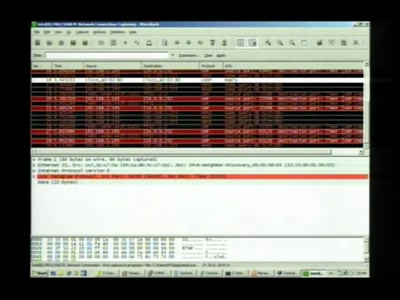
Cisco IOS attack and defense
The State of the Art
40 min
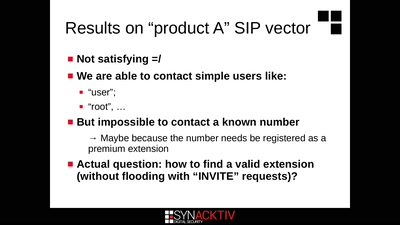
Intercoms Hacking
Call the frontdoor to install your backdoors
59 min
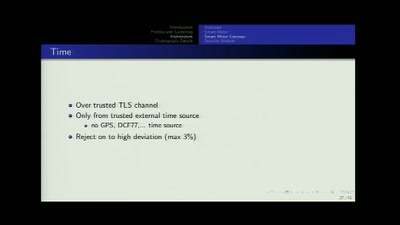
SmartMeter
A technological overview of the German roll-out
33 min
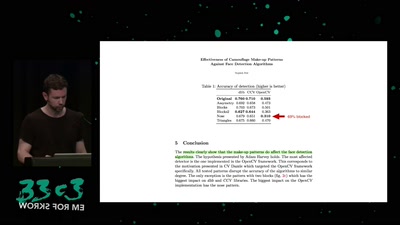
Retail Surveillance / Retail Countersurveillance
50 most unwanted retail surveillance technologies / 50 most…
36 min
Understanding the Snooper’s Charter
Theresa May’s effort to abolish privacy

63 min
Dissecting HDMI
Developing open, FPGA-based capture hardware for conference…
37 min
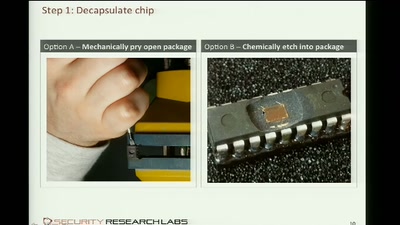
Cracking the MSP430 BSL
Part Two

60 min
Building a high throughput low-latency PCIe based SDR
Lessons learnt implementing PCIe on FPGA for XTRX Software…
38 min
NOC Review
NOC Review about the 29C3
63 min
Building Custom Pinball Machines
What you need and how it works. An experiences report
30 min
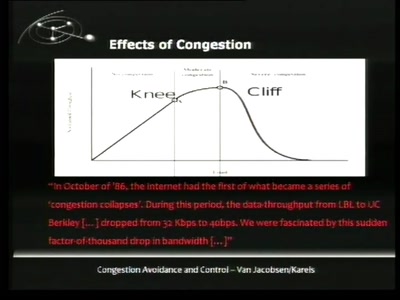
TCP Denial of Service Vulnerabilities
Accepting the Partial Disclosure Challenge

33 min
Eavesdropping on the Dark Cosmos
Dark Matter and Gravitational Waves

61 min
Handschellen hacken
Essentielles Grundwissen für alle, die nichts zu verbergen…
56 min