Search for "Inc.)" returned 11620 results
40 min
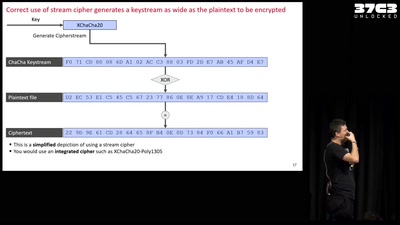
Unlocked! Recovering files taken hostage by ransomware
Decrypting files hijacked by the "second most used…

27 min
The law and leaky abstractions
In what ways can laws influence the security of society.
26 min
Der 33 Jahrerückblick
Technology and Politics in Congress Talks, from 1984 to now

28 min
Mexican Botnet Dirty Wars
Bots are waging a dirty war in Mexican social media.
49 min
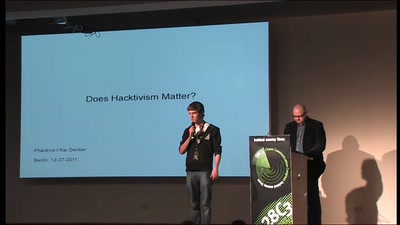
Does Hacktivism Matter?
How the Btx hack changed computer law-making in Germany
62 min
The Story of The Hacker Foundation
Challenges of Organizing a Foundation for Hackers in the USA
52 min
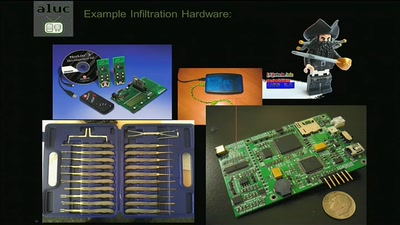
The engineering part of social engineering
Why just lying your way in won't get you anywhere

58 min
The Renaissance of Perl
Was sich in den letzten Jahren bei Perl5 getan hat

58 min
Funkzellenabfrage: Die alltägliche Rasterfahndung unserer Handydaten
Wie wir alle regelmäßig den Behörden ins Netz gehen und wie…
21 min
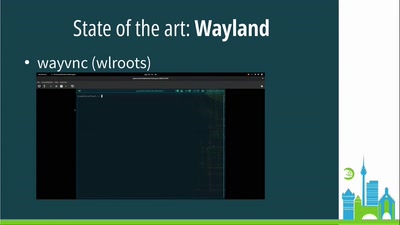
Remote headless Wayland sessions on GNOME
Talk about the work I've been doing in the last year
48 min
Foreman SCC Manager: Rechenzentrumsautomatisierung von SLES
Verwalten Sie Inhalte von SUSE bequem in Foreman und Katello
56 min
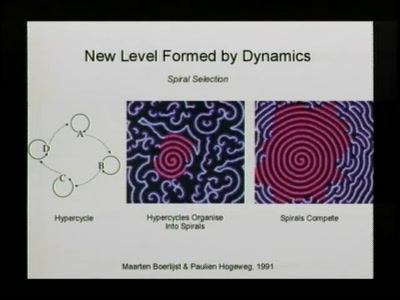
Life & Complexity
Organisation, information and optimisation in real and…
49 min
Mining Search Queries
How to discover additional knowledge in the AOL query logs
48 min
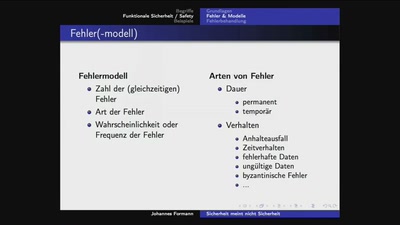
Sicherheit meint nicht Sicherheit und erst recht nicht Verfügbarkeit
Ein kleiner Ausflug in die verschiedenen Begriffswelten und…
61 min
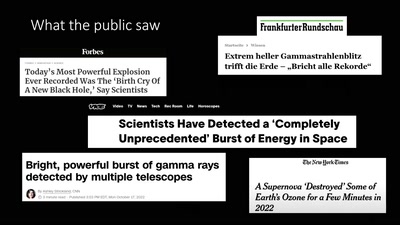
About Gamma-Ray Bursts And Boats
What We (Don't) Know About the Most Energetic Events in the…
35 min
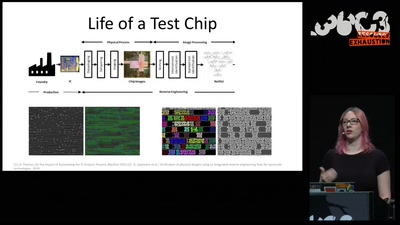
Understanding millions of gates
Introduction to IC reverse engineering for…
58 min
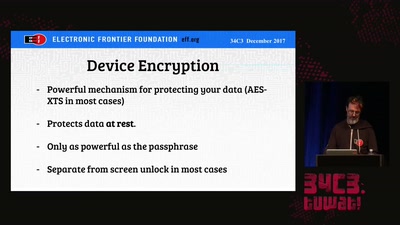
Protecting Your Privacy at the Border
Traveling with Digital Devices in the Golden Age of…

43 min
Drupal as a graphics platform
Implementing graphic API into Drupal with built-in SVG…
40 min
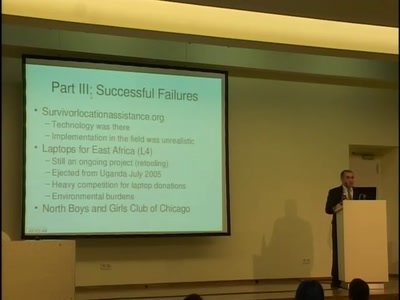
Data Mining Your City
Early lessons in open city data from Philadelphia, PA, USA
26 min
ChokePointProject - Quis custodiet ipsos custodes?
Aggregating and Visualizing (lack of) Transparancy Data in…
32 min
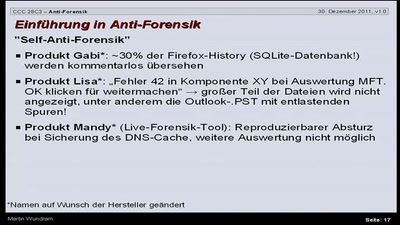
Antiforensik
Einführung in das Thema Antiforensik am Beispiel eines…

39 min
Hurra, diese Welt geht unter!?
Welche kollektiven Erzählungen brauchen wir, um in der…
60 min
Kybernetik und Kontrolle
Von der autoritären Nutzung von Daten in China und anderswo

119 min
CR242: Einmal einschmelzen bitte
Warum modernes CPU-Design uns jetzt in Teufels Küche bringt
49 min