Search for "mh" returned 3041 results
61 min
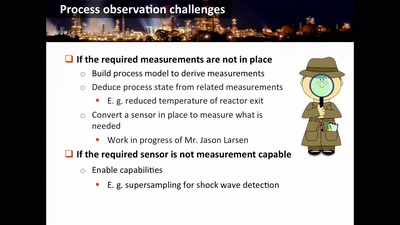
Damn Vulnerable Chemical Process
Exploitation in a new media
35 min
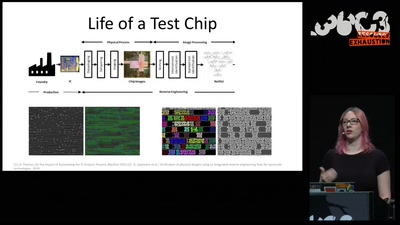
Understanding millions of gates
Introduction to IC reverse engineering for…
30 min
On Computing Numbers, with an Application to Problems of our Society
Journalism ♥ Computer Science
62 min
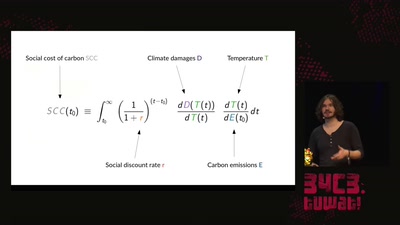
A hacker's guide to Climate Change - What do we know and how do we know it?
An introduction to the basics of climate research and what…
29 min
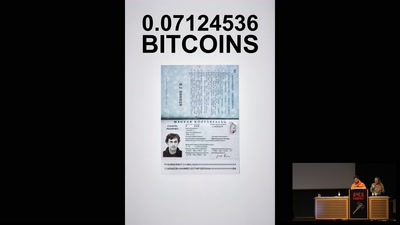
Ecstasy 10x yellow Twitter 120mg Mdma
Shipped from Germany for 0.1412554 Bitcoins
60 min
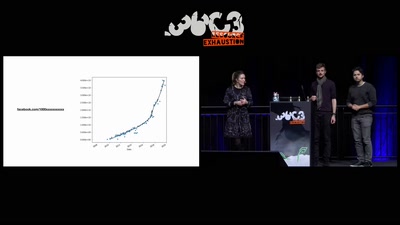
Inside the Fake Like Factories
How thousands of Facebook, You Tube and Instagram pages…
60 min
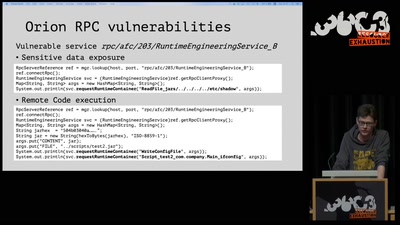
On the insecure nature of turbine control systems in power generation
A security study of turbine control systems in power…

60 min
Quantum Cryptography
from key distribution to position-based cryptography
58 min
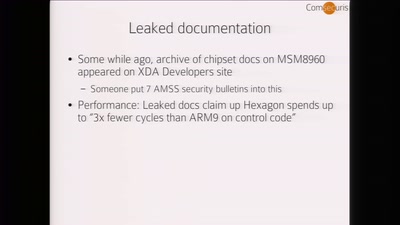
Baseband Exploitation in 2013
Hexagon challenges

61 min
Quantenphysik und Kosmologie
Eine Einführung für blutige Anfänger
29 min
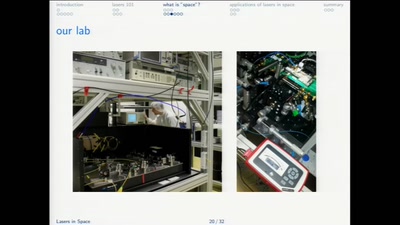
lasers in space
more than just pew pew!
35 min
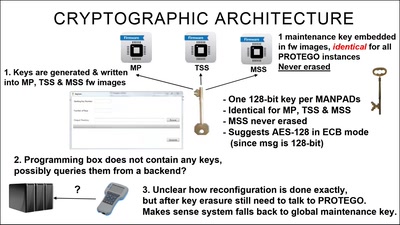
Harry Potter and the Not-So-Smart Proxy War
Taking a look at a covert CIA virtual fencing solution

40 min
What is this? A machine learning model for ants?
How to shrink deep learning models, and why you would want…

55 min
What is Good Technology?
Answers & practical guidelines for engineers.
63 min